D-Fend Solutions, a leader in field-proven radio frequency (RF) cyber-driven, non-kinetic, non-disruptive counter-drone takeover technology, deployed its EnforceAir system to support airspace security operations during the recent 55th Annual JUNO Awards in Hamilton, Ontario. EnforceAir’s non-kinetic, non-jamming approach allowed communications and authorized drones to remain operational while safeguarding against rogue drone threats.
Held at TD Coliseum in Hamilton, Ontario, on March 29, the JUNO Awards hosted approximately 19,000 attendees inside the venue, with several thousand more in surrounding areas. Given the presence of VIPs, government officials, and large public crowds, maintaining secure, coordinated airspace operations was a critical component of the event’s overall safety strategy.
“Large-scale public events like the JUNO Awards pose uniquely complex security challenges, where maintaining safe and controlled airspace is just as critical as securing the ground,” said Zohar Halachmi, chairman and CEO of D-Fend Solutions. “This EnforceAir deployment demonstrates how new generation advanced RF-Cyber technology can seamlessly integrate into existing operations, providing real-time awareness and actionable intelligence without interfering with communications and operations, including authorized drones in the airspace.”
Securing Mass Gatherings
RF-Cyber is becoming a standard technology for mass gatherings as its no interference approach avoids jamming that can disrupt communication networks. The technology provides a non-intrusive security layer that does not disrupt sensitive operational systems that may be used by officials and media crews at such events.
Supporting Local Police Drone Operations
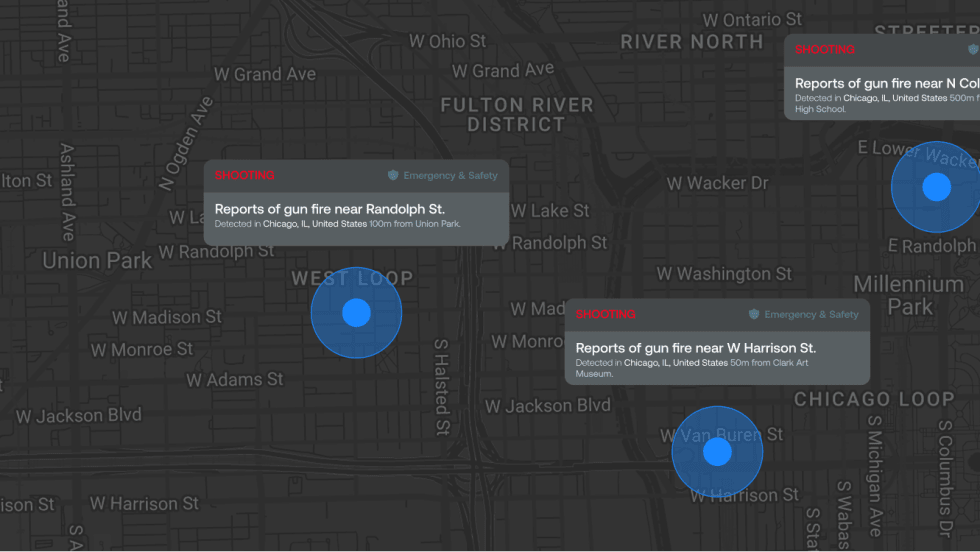
As part of a joint RPAS unit, D-Fend Solutions’ EnforceAir2 system (EA2) was integrated directly into the Hamilton Police Emergency Operations Centre and provided a common operational picture with real-time airspace awareness.
The system supported Hamilton Police drone operations by detecting, locating, and identifying unauthorized or potentially malicious drones, distinguishing between authorized and unauthorized drones in real time through automated identification, and enabling coordinated response efforts.