Cloud technology is a force to be reckoned with in the field of public safety and can provide secure, cost-effective solutions to meet the technological needs of law enforcement.
Technological advances in recent decades have provided law enforcement professionals with the tools needed to increase efficiency and more effectively serve the public. Agencies are now equipped to manage dispatch, records, corrections, and other key public safety functions with innovative equipment and software, storing vast amounts of crucial data either in their own facilities using on-premises software packages and servers or in the cloud.
On-premises servers are used by many law enforcement agencies nationwide. But this system is not necessarily a viable or economical option for every agency. Fortunately, an alternative has emerged for agencies that don't want to use on-premises servers, cloud technology.
What is the Cloud?
The cloud is a Web-based network of servers used to store and access data and software through the Internet.
Web-based data storage is a major component in cloud technology, as most if not all, Web-based software solutions utilize the cloud to store and access data. Some vendors utilize the cloud exclusively for this purpose and provide the participating agencies with access to a database through a desktop application. In these cases, the desktop client on each individual computer pulls data from and pushes data to the database as the user performs various tasks. This method functions similarly to programs such as iTunes and Skype. The software itself is located on the individual desktop or laptop, but remains in constant communication with data in the cloud.
An alternative option involves hosting an interface, with the data within the cloud, and then accessing both using a standard Internet browser such as Google Chrome or Mozilla Firefox. This browser-based solution operates similarly to online banking platforms or social media websites. The user simply logs in on the vendor's website to access agency data. All tasks are then performed within the browser window. Spillman Technologies' Web-based solution, Spillman Nova, falls into this category.
Benefits of the Cloud
One of the benefits of utilizing either type of Web-based solution to meet public safety needs is they are often more cost effective for agencies that might not be able to accommodate an on-premises software system. Cloud-based products often fall under a subscription-based Software-as-a-Service (SaaS) pricing structure, which allows solutions to be tailored to fit the size of the agency, eliminating unnecessary spending. Law enforcement agencies can benefit from utilizing modern technology without spending a vast portion of their budgets to purchase and maintain large physical databases on their premises.
Both desktop- and browser-based methods of cloud computing provide agencies with the benefit of consistent access to the most current public safety tools. Frequent software updates can be distributed instantly through the cloud with no hardware installation required.
For agencies using desktop-based platforms, the process of updating can be as simple as checking for and downloading updates or even configuring software settings to automatically install updates as soon as they are released by the vendor.
The process of updating browser-based software is essentially effortless for agency users because no updates are required on the user's end. The vendor simply updates the application within the cloud and every participating agency gains immediate access to the new technology, with no waiting lists and no disruptions in service.
Both methods can prove beneficial to law enforcement agencies because the SaaS format generally includes access to all software updates in the cost of the subscription. Agencies are able to remain constantly abreast of the latest technological developments, regardless of location, size, hardware, and the date the software was originally implemented.
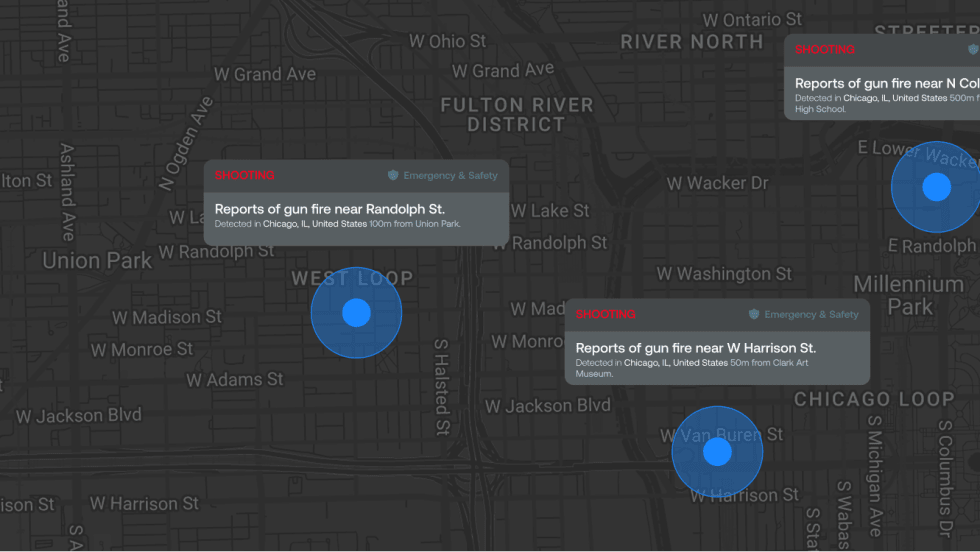
The cloud-based solution model also allows law enforcement personnel to utilize cutting-edge technology and data wherever and whenever needed. Any device with an Internet connection can provide users with access to mission-essential information and tools while serving out in the community. Field officers can use Web-enabled laptops in their patrol vehicles to access name and vehicle records during a routine traffic stop, check on past events associated with an address before ever approaching the door, or easily type and submit reports after finishing with a call, capturing and saving accurate data while the details of the incident are fresh.
Mobile browser-based interfaces and downloadable apps make it possible to also maximize agency efficiency and data accuracy using tablets and smartphones. Thorough integration with the hardware and software built into these devices allows users to take advantage of the tools they are already carrying around in their pockets such as the camera, microphone, GPS, text-to-speech capability, and near-field communication (NFC) capability. For example, an officer could use the camera built into a smartphone to capture several images of damaged or vandalized property and then upload those images directly to the agency's database in the cloud, giving all other agency personnel instant access to the scenes in front of them. The officer could then verbally dictate a statement using the built-in microphone and text-to-speech software before uploading the completed report into the cloud.
All of these capabilities can be utilized to benefit agencies and communities, but one of the greatest benefits of cloud-based public safety technology is that it enables law enforcement agencies to take their data beyond the fields of capture and storage alone. By placing data in the ever-growing and evolving environment of the cloud, users are able to search and organize the information quickly, easily, and in innumerable configurations, maximizing the value of data they work so hard to collect.
Is It Secure?
Much of the conversation surrounding cloud computing in public safety operations has often been dominated by one question: Is data stored in the cloud secure? Law enforcement agencies have expressed concern that because cloud databases are stored and accessed through the Internet it may be difficult to maintain the level of security required by the FBI's Criminal Justice Information System (CJIS).
In 2012, the FBI stated that cloud-based technology can be utilized effectively within the sphere of public safety, as long as the software vendors maintain standards of CJIS compliancy. Those requirements initially posed challenges for vendors, but process improvements and fine-tuning in the years since have allowed law enforcement agencies to successfully adopt secure, cloud-based solutions.
Cloud technology is clearly a force to be reckoned with in the field of public safety. As software vendors provide secure, cost-effective solutions to meet the technological needs of law enforcement, agencies are constantly finding new ways to make the most of their data. While on-premises solutions meet the needs for many law enforcement agencies, the development of public safety technology within the cloud provides another viable option. It falls to each individual agency to decide what kind of solution best fits the needs of its personnel and community.
Morgan Hardy is a marketing writer for Spillman Technologies.