Cybercriminals Targeting Police, Hospitals, Schools for Ransom
But if this happens to your agency, don't expect the ransom to be $350. So-called ransomware attacks have surged so sharply that the FBI says hacking victims in the United States have paid more than $209 million in ransom payments in the first three months of this year, compared with $25 million in all of 2015. The FBI has not reported any arrests.
Three weeks ago, a debilitating digital virus spread quickly in computer networks at three Southern California hospitals owned by Prime Healthcare Services, encrypting medical and other data so it was impossible to access.
Using a pop-up window, unidentified hackers demanded about $17,000 in the hard-to-trace cybercurrency called bitcoin for the digital key to unlock the data.
The attempted extortion by criminal hackers was the latest case of what the FBI says is a fast-growing threat and law enforcement agencies are a favorite target.
In March 2015, for example, the Lincoln County Sheriff's Department in coastal Maine paid about $350 in bitcoin for the key to its encrypted data after a malware attack. After the data was unlocked, Western Union reimbursed the county for the ransom payment, according to a county official who described the transaction, the Los Angeles Times reports.
That followed similar reported attacks on law enforcement in Tewksbury, Mass.; Midlothian, Ill.; Dickson County, Tenn.; Collinville, Ala.; and Durham, N.H. Some police chiefs refused to pay, saying they had backed up their data or it wasn't crucial.
But if this happens to your agency, don't expect the ransom to be $350. So-called ransomware attacks have surged so sharply that the FBI says hacking victims in the United States have paid more than $209 million in ransom payments in the first three months of this year, compared with $25 million in all of 2015. The FBI has not reported any arrests.
Experts say agencies should train employees not to open digital attachments or to click on unfamiliar weblinks in emails that might contain viruses or other malware. They also should back up critical data and use up-to-date virus detection software.
More Patrol

Why Tennessee’s New Deadly Force Law Matters Beyond Tennessee
Tennessee’s new deadly force law is more limited than many may realize. Effective July 1, 2026, the law applies to a person who is not engaged in conduct that would constitute a felony or a Class A misdemeanor and who is in a place where the person lawfully resides. But it could have far-reaching influence.
Read More →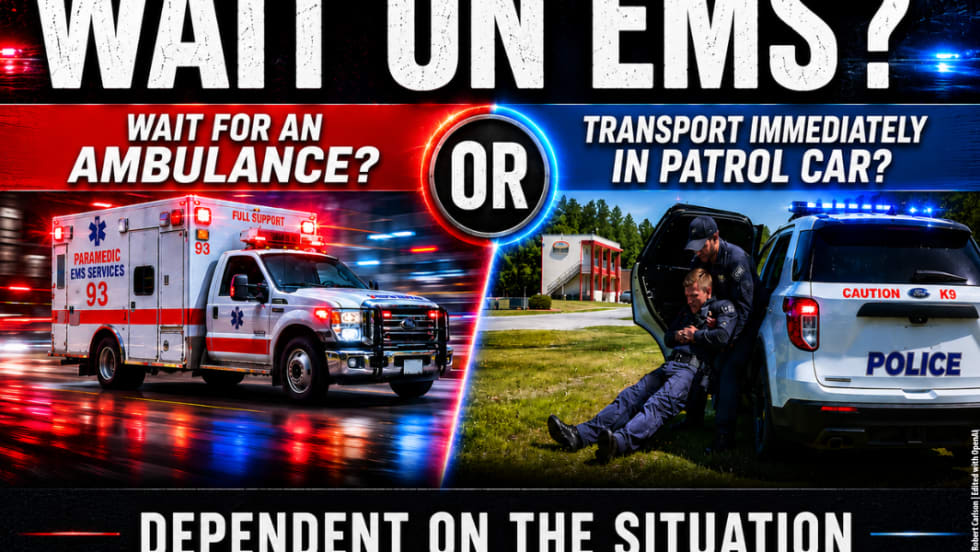
When Do You Transport a Wounded Officer by Police Vehicle?
Time-sensitive injuries like penetrating trauma mean a wounded officer needs to reach a trauma center as soon as possible, and in some cases, that means transporting by police vehicle rather than waiting for EMS. What are the factors to consider in making that transport decision?
Read More →
Safariland Solis Rethinks Concealable Duty
What if Level I retention didn’t require a full duty rig? Safariland’s Solis delivers trusted ALS security in a streamlined OWB platform built for administrative and plainclothes professionals who need protection without the bulk.
Read More →
5 Things to Know When Buying Backup Lights for Patrol Use
What is the value of a backup light, and what do you need to consider when selecting one? These smaller lights are invaluable as a secondary or special-purpose light and can be easily carried in a pocket or clipped to MOLLE gear, a key chain, shirt, or a vest.
Read More →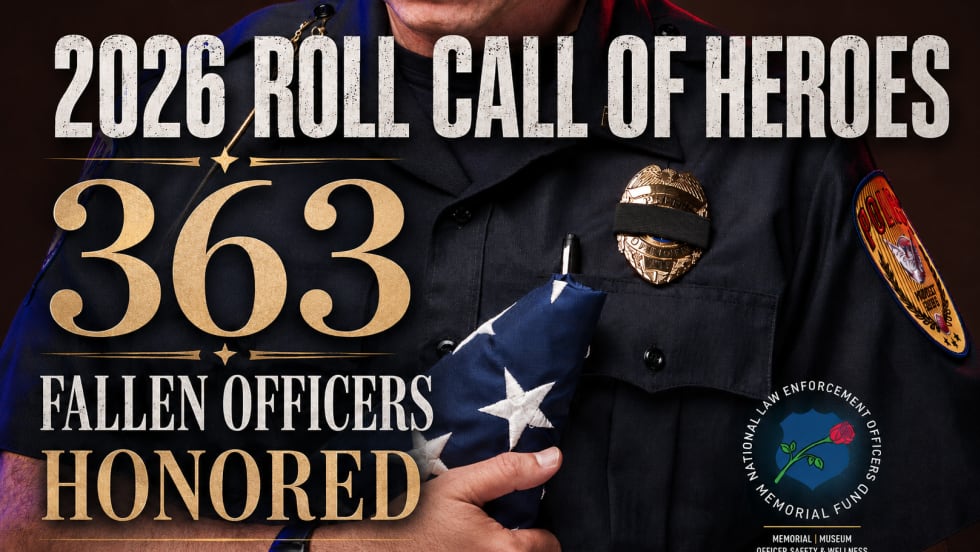
363 Fallen Officers Honored During National Police Week
In case you missed NELOMF’s annual Candlelight Vigil, here are all 363 names of the fallen officers whose names were added to the National Law Enforcement Officers Memorial this year.
Read More →
NYPD Officers Who Responded Quickly During IED Incident Recognized as NLEOMF Officers of the Month
Chief Aaron Edwards and Sgt. Luis Navarro were recognized by NLEOMF as Officers of the Month for their response during an IED incident and their actions that helped prevent harm to the public.
Read More →
National Police Survey Reveals How Americans View Policing Today
A new national survey offers a comprehensive look at how Americans view policing. The study uncovers public sentiment toward local vs. federal police, communications, crisis response, the use of AI in policing, and more.
Read More →
Streamlight TLR-7 X Selected as Standard Issue Pistol Light by Canadian Federal Police
The Canadian Federal Police will be adding a new duty pistol system, which will include Streamlight’s TLR-7 X and a Glock 45 MOS 7 pistol with a red dot sight.
Read More →
Fallen Law Enforcement Officers from Across the Country to be Honored During 38th Annual Candlelight Vigil on May 13th in Washington, D.C.
The National Law Enforcement Officers Memorial Fund (NLEOMF) will honor 363 fallen officers who have died in the line of duty as their names are added to the National Law Enforcement Officers Memorial during the annual Candlelight Vigil on May 13.
Read More →
What Should Be in Your IFAK?
What should every officer include in an IFAK? Sydney Vail, M.D., a veteran trauma surgeon and former SWAT surgeon, explains which components are needed and which are not, and stresses training.
Read More →

