Here's Why the FBI Forcing Apple to Break Into an iPhone Is a Big Deal
When U.S. Magistrate Sheri Pym ruled that Apple must help the FBI break into an iPhone belonging to one of the killers in the San Bernardino, CA, shootings, the tech world shuddered. Apple's CEO doesn't want to create a "backdoor" to let the FBI in.
When U.S. Magistrate Sheri Pym ruled that Apple must help the FBI break into an iPhone belonging to one of the killers in the San Bernardino, CA, shootings, the tech world shuddered. Why? The battle of encryption "backdoors" has been longstanding in Silicon Valley, where a company's success could be made or broken based on its ability to protect customer data, reports USA Today.
The issue came into the spotlight after Edward Snowden disclosed the extent to which technology and phone companies were letting the U.S. federal government spy on data being transmitted through their network.
Since Edward Snowden's whistleblowing revelations, Facebook, Apple and Twitter have unilaterally said they are not going to create such backdoors anymore.
So here's the "backdoor" the FBI wants: Right now, iPhone users have the option to set a security feature that only allows a certain number of tries to guess the correct passcode to unlock the phone before all the data on the iPhone is deleted. It's a security measure Apple put in place to keep important data out of the wrong hands.
Federal prosecutors looking for more information behind the San Bernardino shootings don't know the phone's passcode. If they guess incorrectly too many times, the data they hope to find will be deleted.
That's why the FBI wants Apple to disable the security feature. Once the security is crippled, agents would be able to guess as many combinations as possible.
Kurt Opsahl, general counsel for the Electronic Frontier Foundation, a San Francisco-based digital rights non-profit, explained that this "backdoor" means Apple will have to to write brand new code that will compromise key features of the phone's security. Apple has five business days to respond to the request.
What does Apple have to say about this? Apple CEO Tim Cook said late Tuesday that the company would oppose the ruling. In a message to customers published on Apple's website, he said: "We can find no precedent for an American company being forced to expose its customers to a greater risk of attack. For years, cryptologists and national security experts have been warning against weakening encryption. Doing so would hurt only the well-meaning and law-abiding citizens who rely on companies like Apple to protect their data."
Back in December, Cook defended the company's use of encryption on its mobile devices, saying users should not have to trade privacy for national security, in a broad interview with 60 Minutes. In the interview, Cook stood by the company's stance of refusing to offer encrypted texts and messages from users.
What does this mean for the next time the government wants access? The order doesn't create a precedent in the sense that other courts will be compelled to follow it, but it will give the government more ammunition.
What now? This could push the tech companies to give users access to unbreakable encryption. To some extent, it's already happening. Companies like Apple and Google — responding to consumer demands for privacy — have developed smart phones and other devices with encryption that is so strong that even the companies can't break it.
More Technology
How Patrolfinder Uses Data to Make Streets Safer
Law enforcement agencies have long relied on instinct and routine to optimize patrols. Patrolfinder uses data to help agencies see where officers go — and where they don’t — to improve visibility and maximize coverage.
Read More →
Crime Prevention by Merging Tech with Human Intervention
Elite Interactive Solutions tackles crime prevention with technology and human intervention, working closely with local police to provide insights when a response is needed. The key is to blend the latest in remote video monitoring, artificial intelligence, and a well-trained agent with eyes on the scene.
Read More →
Case Study Details Integration of Body-Worn Cameras with CAD
The Billerica Police Department (Massachusetts) improved transparency and accountability, sharpened evidence management, and reduced manual hours by integrating Axis Communications body-worn cameras with its Computer-Aided Dispatch (CAD) system.
Read More →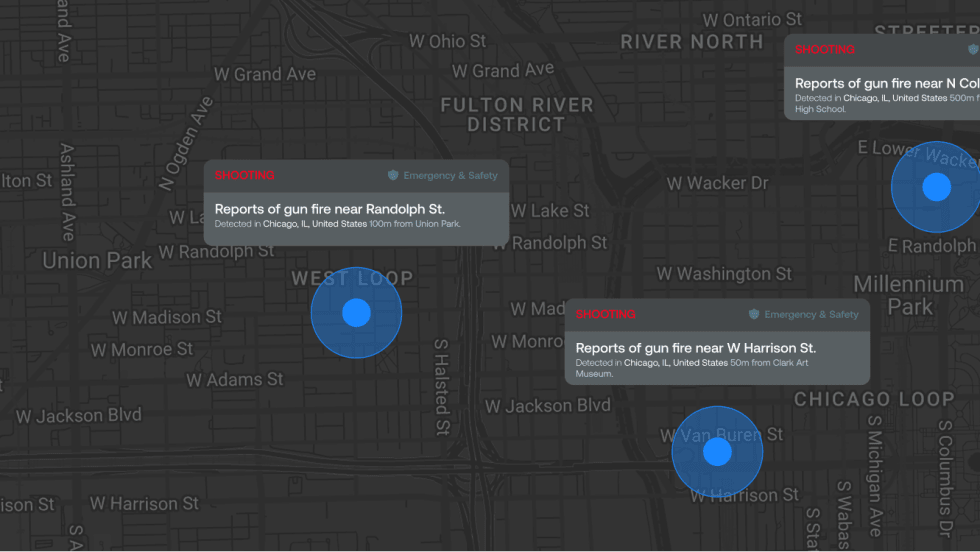
ZeroEyes Public Safety Alerts Integrates Samdesk for Real-Time Risk Detection and Awareness
ZeroEyes has integrated Samdesk into its Public Safety Alerts platform to deliver faster, verified intelligence to help organizations understand emerging risks and respond quickly.
Read More →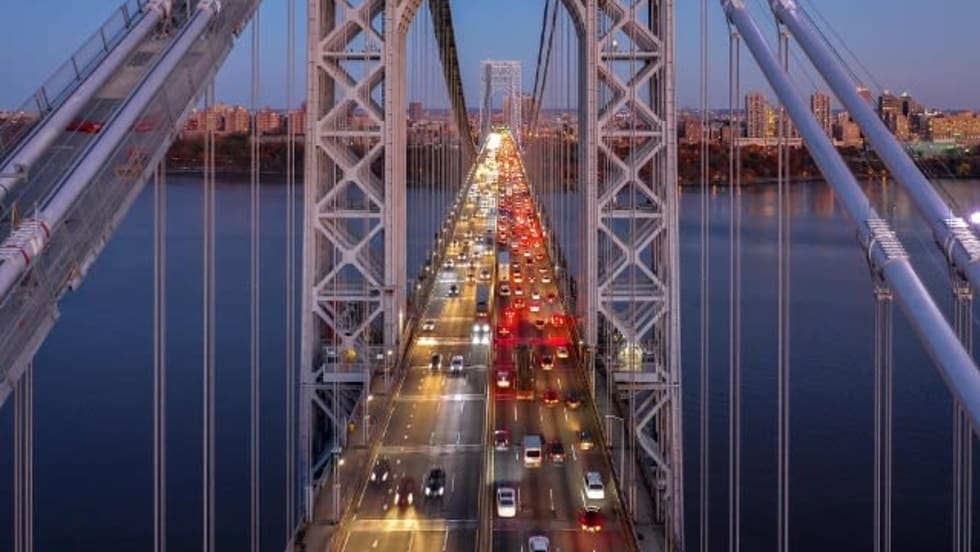
NJ Police Department Combines Strong Technology & Public Safety Strategy
The Fort Lee Police Department in New Jersey has modernized with Genetec Security Center, including video management, automatic license plate recognition (ALPR), and Clearance digital evidence management.
Read More →
Pimloc & Dynamic Workflow Solutions Partner to Deliver Data Management and Automated Redaction
The joint redaction solution from Pimloc and Dynamic Workflow Solutions helps agencies reduce FOIA response time and compliance risk by automatically redacting faces, license plates, and other sensitive information from digital evidence.
Read More →
The University of Alabama Rolls Out Couter-Drone Technology
The University of Alabama is using D-Fend Solutions as a counter-drone technology supplier for campus and game-day airspace security. The University integrates D-Fend’s EnforceAir into its Emergency Operations Center (EOC), utilizing a unified command framework to collaborate with local, state, and federal partners during major events.
Read More →
Motorola Solutions Now Part of the Cyber Threat Alliance
Motorola Solutions is now part of the Cyber Threat Alliance, the first formally organized nonprofit group of cybersecurity practitioners that work together in good faith to share threat information and improve global defenses against advanced cyber adversaries.
Read More →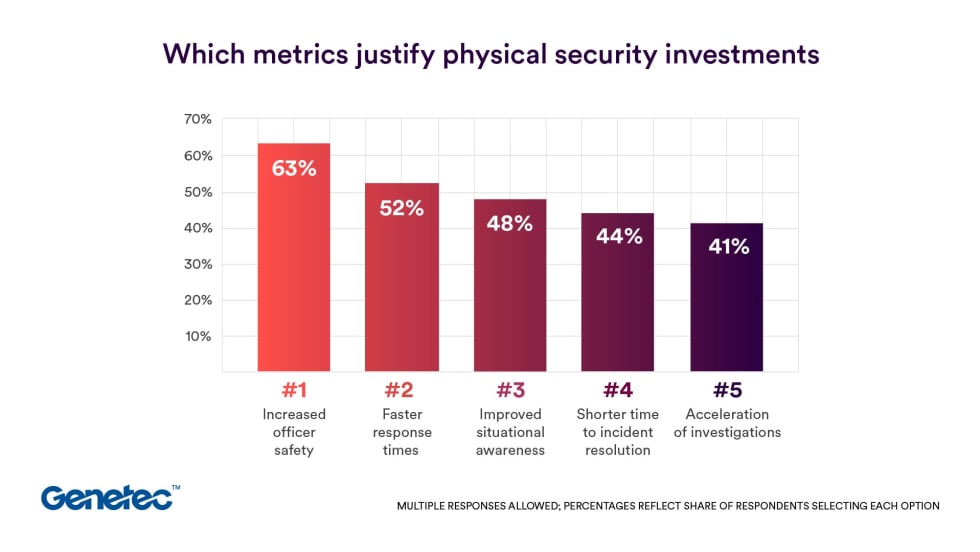
Genetec 2026 State of Physical Security Report Reveals Public Safety Priorities & Challenges
Survey results from Genetec’s 2026 State of Physical Security Report highlight the demand for integrated systems that improve response times and reduce investigative workload. Nearly nine in 10 respondents said they use security data to help keep officers safe.
Read More →
Flock Safety Introduces Audit Assistance, Its Latest Trust & Compliance Tool
Audit Assistance is the latest tool in the Flock Trust & Compliance suite, a first-of-its-kind set of products and services that provides communities with guardrails and customization for accountability, transparency, and responsible use of the Flock platform.
Read More →