Cyber Terrorism: Preventing Online Assault
Hackers constantly target law enforcement. Whatever the intent, with our dependence on technology it's more important than ever that police agencies protect themselves against cyber terrorist attacks.

Photo: Mark W. Clark
Hackers constantly target law enforcement. According to the head of the Los Angeles Sheriff's Department's Data Security team, hackers attempt to infiltrate the agency's systems at least once every day—locally and from other states, countries, and continents. But the reasons for the attempts have changed. No longer merely games to demonstrate code-cracking skills "for fun or for fame," motivations are more likely to be nefarious now. Reasons could be financial or political. Whatever the intent, with our dependence on technology it's more important than ever that police agencies protect themselves against cyber terrorist attacks.
Ferguson
For an example of cyber terrorism perpetrated against law enforcement you need only look to the recent attacks by the collective known as Anonymous after a police officer in Ferguson, Mo., shot 18-year-old Michael Brown.
These loosely linked anarchist hackers first took to Twitter and urged citizens to threaten officers during protests. Next they caused the city's Web servers to crash, which took out department radios and forced law enforcement officers to communicate via text. Then they started releasing law enforcement-sensitive information. And it got personal.
Early on in the investigation, officials decided not to release the identity of the officer who shot Brown. In a bid to bully the police into releasing the name, an Anonymous member posted online the home address and phone number of St. Louis County police Chief Jon Belmar. Then they posted photos of his family as well as their names. The succession of creepy posts stopped just short of encouraging people to use this information to attack the chief and his family members.
When law enforcement didn't comply with the hacker group's demands, a member of Anonymous released an officer's name based on information culled from the Internet. It was incorrect information, but it demonstrates cyber terrorists' willingness to find and make sensitive information public and follow through on other threats against the government.
This is just one reason why protecting the security of law enforcement networks and data is so important. Large-scale attacks on major law enforcement infrastructure could compromise the safety of officers and the public. Here's what can be done to prevent such attacks.
Depend on Dedicated Experts
"I see attacks on a daily basis. It's about being vigilant and making sure security is in place to prevent these things from happening," says Soheil Naimi, information security officer for the Los Angeles Sheriff's Department. As the man in charge of his agency's cyber security, he makes sure multiple layers of protection exist between a hacker and the sensitive information housed on the network, the so-called onion model. This includes firewalls, antivirus software, and intrusion detection systems. "I'm always working hard to make sure our onion is in good shape," he says. And he and his co-workers have the time to do so.
Naimi acknowledges that not every department has the budget or need for a six-man unit devoted to cyber security, as he has. But he's adamant that every agency needs a unit or at least a person devoted to maintaining cyber security. If your agency is too small to hire someone fulltime, you can even hire someone from an outside company to work there part-time, he suggests. Just make sure you fully vet the company.
Deputy Superintendent John Daley, chief technology officer of the Boston Police Department, agrees wholeheartedly that cyber security requires special attention and can't be left as an afterthought to be handled by an already busy officer. "This is hard stuff even for people within tech to keep up with," he says. "There's a lot going on out there, and it's a challenge."
Utilize Resources
Making use of available resources is one way to stay on top of all of the cyber threats facing law enforcement today. A major resource everyone in law enforcement can now take advantage of is the FBI's new Cyber Shield Alliance. Launched in January, this extensive Website is designed as a one-stop-shop for anyone in policing looking for information about threats to cyber security. Site registration is available to sworn and non-sworn employees.
"It's a whole government approach. To make it easier to get intel, we've corralled resources from the DHS, FBI, DOD, Secret Service, and the Multi-State Information Sharing and Analysis Center (MS-ISAC)," says an FBI expert in cyber security who's an agent with the Bureau's Computer Intrusion Violations division. "Through the Cyber Shield Alliance Website, accessed via CJIS, you click on the 'intel reports' link and you can see a myriad of sources in one place so you can get a better understanding of the threatscape out there."
In addition to research on threats to guard against, if your agency does suffer a successful attack the Cyber Shield Alliance portal site serves as a central location to report a data breach. Submit a report through what is called e-Guardian and it will reach the FBI's Cyberwatch 24/7 call center. All the relevant federal agencies will be immediately notified so they can respond as needed without any additional calls.
Most people who visit the site will be those who maintain law enforcement networks, but the Cyber Shield Alliance can provide useful information to anyone interested and is also a resource for cybercrime investigators to find information about the newest criminal activities being perpetrated online.
Off the Web, members of other agencies can also provide a great source of intelligence. "Because we want to keep up to date with technology, we work with task forces, the FBI, the Secret Service, and the local DA's office," says Daley.
It might seem odd to work with the district attorney's office, but Daley says it's a matter of taking advantage of available resources. Investigators are able to share the DA's office's equipment and training, thereby protecting everyone's interests.
Daley is also a big proponent of establishing partnerships with local businesses, noting that companies have the added incentive of a "bottom line interest in keeping up on emerging threats." Under his leadership, the Boston Police Department has shared information about cyber threats within the business community for years and both sides find it mutually beneficial.
Get Training
With so many changes constantly taking place in technology, it's imperative that the people tasked with maintaining agencies' cyber security keep current with ongoing training. The Cyber Shield Alliance provides online courses, and is in the process of developing an extensive program that will provide certification in specific areas.
"The first phases will be online with actual scenario-based situations in virtualized environments, so individuals will be able to demonstrate that they understand the material," explains an FBI expert. "The final phase will culminate with a two-week capstone hosted at either an FBI or other federal service facility. You will sit in an environment where you'll collaborate with other law enforcement members in a cyber threat scenario and demonstrate skills used to work a case from beginning to end."
While these cyber investigative certification courses are being developed, in the meantime you can take other free online courses through the Cyber Shield Alliance that include both information technology industry classes and the FBI's own law enforcement-specific courses.
While the person or people dedicated to protecting your agency's cyber security need to be up on any new trends in this field, it's also important for all officers to be aware of any dangers. And it doesn't need to be complicated. LASD simply puts out a monthly e-newsletter to alert all employees to any new tips and threats, as well as reminders of how to be safe.
Not everyone is an IT expert, but virtually every employee at a law enforcement agency interfaces with the network nowadays. The average officer needs to be aware of the small mistakes that can create big problems for cyber security. Clicking on one wrong link or being careless with password information can spell real trouble for an entire department.
"You can have all the proper technical safeguards in place, but the most common point of compromise is the end user," warns Daley. "If you can educate the end user, you're so much better off in the long run. It's a matter of educating and preventing those types of common mistakes that can be made."
RESOURCES:
More Technology
How Patrolfinder Uses Data to Make Streets Safer
Law enforcement agencies have long relied on instinct and routine to optimize patrols. Patrolfinder uses data to help agencies see where officers go — and where they don’t — to improve visibility and maximize coverage.
Read More →
Crime Prevention by Merging Tech with Human Intervention
Elite Interactive Solutions tackles crime prevention with technology and human intervention, working closely with local police to provide insights when a response is needed. The key is to blend the latest in remote video monitoring, artificial intelligence, and a well-trained agent with eyes on the scene.
Read More →
Case Study Details Integration of Body-Worn Cameras with CAD
The Billerica Police Department (Massachusetts) improved transparency and accountability, sharpened evidence management, and reduced manual hours by integrating Axis Communications body-worn cameras with its Computer-Aided Dispatch (CAD) system.
Read More →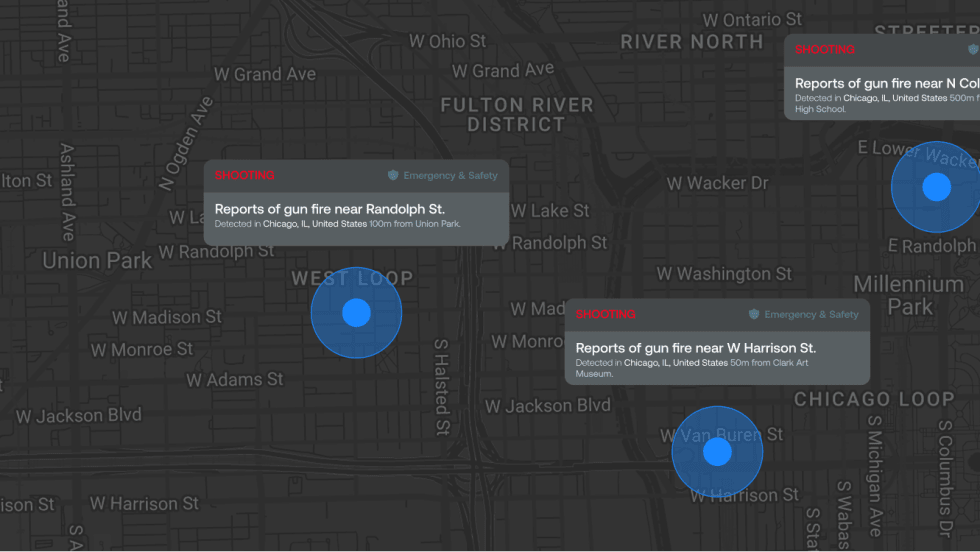
ZeroEyes Public Safety Alerts Integrates Samdesk for Real-Time Risk Detection and Awareness
ZeroEyes has integrated Samdesk into its Public Safety Alerts platform to deliver faster, verified intelligence to help organizations understand emerging risks and respond quickly.
Read More →
NJ Police Department Combines Strong Technology & Public Safety Strategy
The Fort Lee Police Department in New Jersey has modernized with Genetec Security Center, including video management, automatic license plate recognition (ALPR), and Clearance digital evidence management.
Read More →
Pimloc & Dynamic Workflow Solutions Partner to Deliver Data Management and Automated Redaction
The joint redaction solution from Pimloc and Dynamic Workflow Solutions helps agencies reduce FOIA response time and compliance risk by automatically redacting faces, license plates, and other sensitive information from digital evidence.
Read More →
The University of Alabama Rolls Out Couter-Drone Technology
The University of Alabama is using D-Fend Solutions as a counter-drone technology supplier for campus and game-day airspace security. The University integrates D-Fend’s EnforceAir into its Emergency Operations Center (EOC), utilizing a unified command framework to collaborate with local, state, and federal partners during major events.
Read More →
Motorola Solutions Now Part of the Cyber Threat Alliance
Motorola Solutions is now part of the Cyber Threat Alliance, the first formally organized nonprofit group of cybersecurity practitioners that work together in good faith to share threat information and improve global defenses against advanced cyber adversaries.
Read More →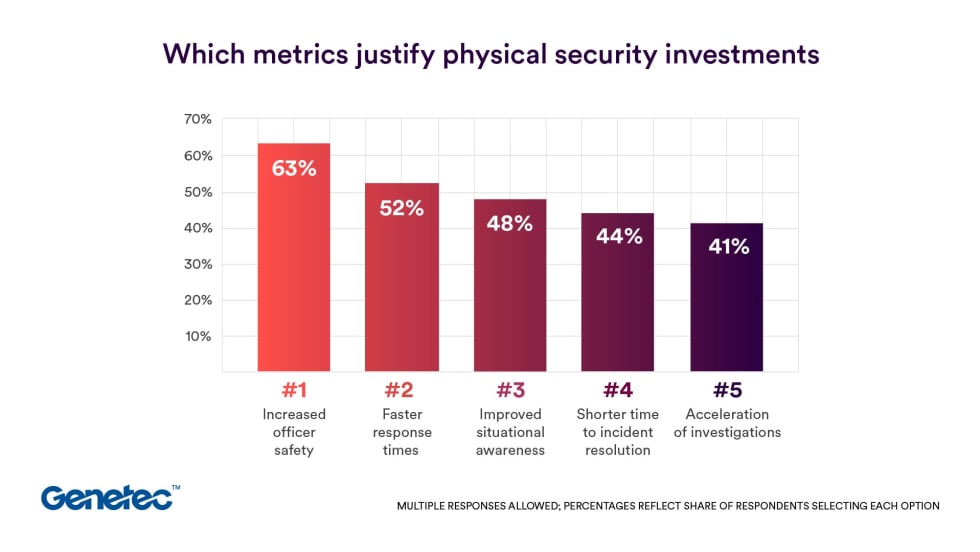
Genetec 2026 State of Physical Security Report Reveals Public Safety Priorities & Challenges
Survey results from Genetec’s 2026 State of Physical Security Report highlight the demand for integrated systems that improve response times and reduce investigative workload. Nearly nine in 10 respondents said they use security data to help keep officers safe.
Read More →
Flock Safety Introduces Audit Assistance, Its Latest Trust & Compliance Tool
Audit Assistance is the latest tool in the Flock Trust & Compliance suite, a first-of-its-kind set of products and services that provides communities with guardrails and customization for accountability, transparency, and responsible use of the Flock platform.
Read More →