20 Years After 9/11: Countering Terrorism on U.S. Soil
Local, state, and federal law enforcement personnel are on the frontlines of counterterrorism efforts in the United States.

Because of New York City’s history of being a target for terror attacks from both foreign and domestic sources, the NYPD maintains one of the nation’s largest and most active law enforcement counter-terror units.
Photo: Getty
In the years following the 9/11 terrorist attacks, there have been numerous attempts of direct violent action made on United States soil by groups or individuals who identify themselves as being sympathetic toward—or outright inspired by—radical Islamist groups such as al Qaeda, Hamas, AQAP, ISIS, Boko Haram, Hezbollah, and the like.
Some—such as the Boston Marathon bombing and the San Bernardino mass shooting—succeeded. Many more like the 2010 Portland Christmas Tree plot and the 2019 attempt on Times Square in New York City were thwarted.
All of these attacks and attempted attacks were planned or perpetrated by what the FBI calls domestic violent extremists (DVEs) and homegrown violent extremists (HVEs)—”two distinct threats, both of which are located primarily in the United States and typically radicalize and mobilize to violence on their own.”
In fact, since 9/11, there has been only one case of a jihadist foreign terrorist organization actively directing a deadly attack inside the United States when Mohammed Al-Shamrani shot and killed three people the Naval Air Station Pensacola in December 2019. Al Qaeda in the Arabian Peninsula (AQAP) claimed responsibility.
What is the current landscape of counterterrorism in the United States, and what can American law enforcement agencies do to help better secure the homeland?
Threat Matrix
The FBI recently restated what it has repeatedly said over the years—that the agency remains concerned that jihad-inspired foreign terrorist organizations (FTOs) such as ISIS and al Qaeda intend to inspire to action surrogate actors to carry out large-scale attacks in the United States.
The agency said that ISIS in particular remains “relentless in its campaign of violence against the United States” and that it “continues to aggressively promote its hate-fueled rhetoric and attract like-minded violent extremists with a willingness to conduct attacks against the United States...”
Meanwhile, there is an increasing concern at the FBI about a possible increase in fatal attacks “perpetrated by anti-government or anti-authority violent extremists, specifically militia violent extremists and anarchist violent extremists.”
Indeed, the FBI has placed an emphasis on the abovementioned domestic violent extremists (DVEs) and homegrown violent extremists (HVEs).
In June, FBI Director Christopher Wray said in testimony before the House Judiciary Committee, “Domestic and homegrown violent extremists are often motivated and inspired by a mix of socio-political, ideological, and personal grievances against their targets, and more recently, have focused on accessible targets to include civilians, law enforcement, and the military.”
Wray added that these individuals—or groups—tend to target symbols or members of the U.S. Government, houses of worship, retail locations, and mass public gatherings.
“Selecting these types of soft targets, in addition to the insular nature of their radicalization and mobilization to violence and limited discussions with others regarding their plans, increases the challenge faced by law enforcement to detect and disrupt the activities of lone actors before they occur,” Wray said.
Identifying Targets
Fred Burton, executive director of the Ontic Center for Protective Intelligence and author of “Ghost: Confessions of a Counterterrorism Agent,” says that terrorist organizations and lone-wolf actors almost always look at more than one target for a planned attack.
Burton was involved in a variety of investigations of terrorist attacks during his career with the Diplomatic Security Service (DSS), including the 1993 bombing of the World Trade Center, which killed six and injured hundreds more. He says, “Sirhan Sirhan tried to look at JFK, but couldn’t get to him, so he picked RFK—Robert F. Kennedy—instead.”
After the 1993 World Trade Center attack, Burton says his investigative group within the DSS started closely examining some of the potential plots the WTC planners chose not to carry out.
“We had a lot of lessons learned that came out of the World Trade Center attack that really opened our eyes into how we try to protect high-value targets,” he explains. “We started delving more into what else could have been looked at because there are always other targets.”
Burton also says that the list of potential targets in the United States has probably expanded in part because of the success law enforcement agencies and other entities have had at hardening targets like federal buildings and diplomatic facilities and the offices and homes of cabinet-level officials, Supreme Court justices, and other “high value” targets.
“In our post-9/11 world, military bases started to lock down, federal buildings got tighter, and so forth,” Burton says. “So, in many ways, the threat has been pushed into and onto the public sector, the private sector, American businesses, and public venues.
“You can’t walk into a diplomatic facility or a foreign resident diplomatic facility on U.S. soil and be successful. It’s much easier to shoot up a soft target in a public venue,” he adds.
Burton also notes that a terrorist’s weapon of choice can be as crude as a vehicle, as was the case in the Bastille Day attack in Nice, France, in 2016. The attacker used a truck to drive into a crowd watching fireworks and killed 87 people and injured more than 400. “That doesn’t take a lot of skill. You just have to be able to have a vehicle of some sort.”
For law enforcement officers with long memories—and an interest in events overseas—such a statement immediately brings to mind a host of other attack possibilities.
In 2004, the Beslan school massacre resulted in the deaths of more than 300 souls, nearly 200 of them children. All but one of the 32 Chechen terrorists responsible were killed in a pitched battle with Russian security forces who stormed the building on the third day of the siege.
In 2005, three bombs exploded in separate locations in London’s Underground rail system, followed moments later by the detonation of a fourth bomb on a double-decker bus outside the British Medical Association building on historic Tavistock Square. Al-Qaeda eventually claimed responsibility for the attack that killed more than 50 people and wounded at least 700 others.
In 2008, 10 members of the Lashkar-e-Taiba terrorist organization conducted coordinated attacks in multiple locations in the coastal city of Mumbai, India. Over the course of three days, nearly 200 innocents were killed in places, including a major train terminal, a hospital for women and children, and a five-star luxury hotel.
Every one of these attacks involved the use of easily obtained small arms and improvised explosive devices, and each incident could very easily be replicated on United States soil.
Consequently, it is incumbent upon every law enforcement entity to critically assess the possible targets in their jurisdiction.
Then, of course, there is the looming prospect of a cyberattack carried out by a terrorist organization—something that requires an entirely different level of sophistication and merits attention in a separate article (see page 56 in this issue).
Suffice it to say that when—not if—state and local law enforcement comes across any indication of a cyberattack by a terror group, federal assets and authorities must be brought to bear.
JTTF
When it comes to partnering with federal agencies in the ongoing effort to defend against terrorism in all forms, the primary point of contact for any state, local, tribal, territorial, and campus law enforcement entity is the FBI’s Joint Terrorism Task Forces (JTTF).
The first JTTF was established in New York City in 1980. Today there are about 200 task forces around the country, including at least one in each of the FBI’s 56 field offices, with hundreds of participating state, local, and federal agencies.
While the FBI remains the nation’s primary law enforcement agency for investigating and preventing acts of domestic and international terrorism, the Department of Homeland Security also plays a pivotal role in the fight.
Following the 9/11 attacks, Congress passed and President George W. Bush signed the Homeland Security Act (HSA) of 2002, creating the DHS and the new cabinet-level position of Secretary of Homeland Security.
DHS has a variety of other responsibilities—securing the nation’s borders, protecting critical infrastructure, and responding to natural disasters among them—but one of the department’s top priorities is to protect Americans from terror threats.
DHS and FBI actively work with local law enforcement to secure large-scale sporting events such as the Super Bowl and other high-profile public gatherings and events.
In addition to providing manpower and infrastructure to supplement the counterterrorism efforts of the nation’s nearly 18,000 police agencies across the country, DHS and FBI are expert in utilizing emerging technology to surveil and interdict planned attacks before they happen.
Increasingly, terror plots are hatched—conceived, discussed, and plotted—among participants via end-to-end encrypted messengers such as WhatsApp and Telegram. While a handful of larger municipal agencies have the manpower and technical acuity to monitor such systems—the NYPD Counterterrorism Bureau, for example—federal law enforcement is often best suited to this task.
State and local police agencies must also rely heavily on federal partners to help in uncovering one of the key linchpins to a successful terror attack—financing activities. The FBI and the Secret Service in particular are adept at watching out for evidence of transactions involving large cash payments, deposits, or withdrawals. These are not just signs of criminal enterprise, but also at times can indicate terrorist funding efforts.
Federal partners are also at the tip of the spear when it comes to the infiltration of suspected terror cells by undercover operatives.
The threat of terrorist attack on United States soil remains a serious matter. The nature of the threat posed by terrorism—both international and domestic in origin—continues to evolve.
In much the same way that the American public was blissfully unaware of what was about to unfold as they turned off the lights and went to sleep on Monday, September 10, 2001, most citizens don’t give much consideration to this persistent threat.
But this threat does indeed persist, and it doesn’t take too much creative thinking to come up with a nearly limitless number of non-state actors who would like nothing better than to be responsible for “the next 9/11.”
Iran has not yet retaliated for the assassination of General Qassem Soleimani—who headed that country’s elite “Quds Force” and was considered by many Iranians to be their version of General Dwight D. Eisenhower—in a drone strike at Baghdad International Airport.
Hezbollah and other terrorist groups in the Middle East continue to threaten attacks on American interests because of our close relationship with Israel.
Propaganda from al Qaeda and ISIS spread on the Internet continues unabated with the stated objective of inspiring individuals to conduct attacks within the United States.
Domestic groups on American soil unabashedly espouse anti-government and/or anti-authority sentiments with thinly veiled threats of violence against the United States government.
In the post-9/11 world, local, state, and federal law enforcement organizations—and individuals—are on the frontlines of counterterrorism efforts in the United States.
Doug Wyllie Is contributing web editor for POLICE.
More Patrol

Why Tennessee’s New Deadly Force Law Matters Beyond Tennessee
Tennessee’s new deadly force law is more limited than many may realize. Effective July 1, 2026, the law applies to a person who is not engaged in conduct that would constitute a felony or a Class A misdemeanor and who is in a place where the person lawfully resides. But it could have far-reaching influence.
Read More →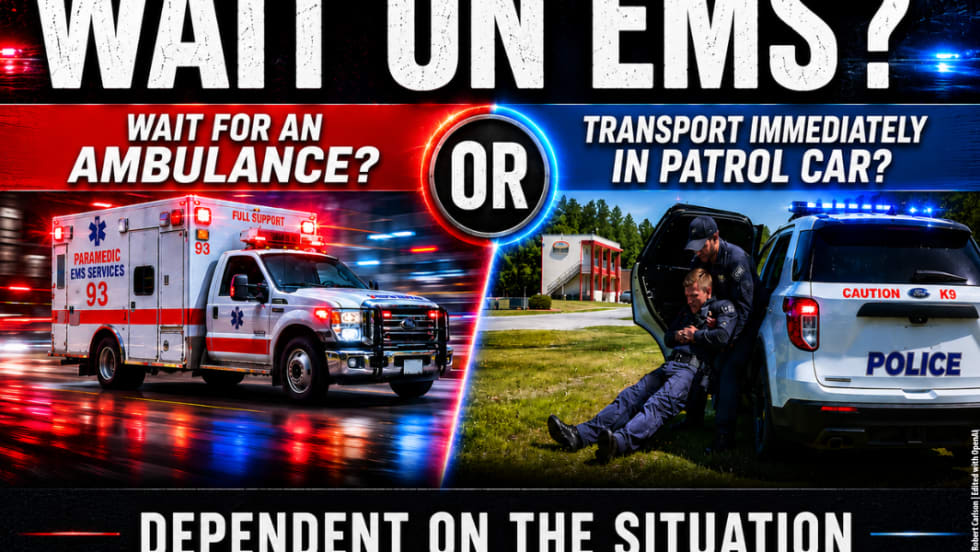
When Do You Transport a Wounded Officer by Police Vehicle?
Time-sensitive injuries like penetrating trauma mean a wounded officer needs to reach a trauma center as soon as possible, and in some cases, that means transporting by police vehicle rather than waiting for EMS. What are the factors to consider in making that transport decision?
Read More →
Safariland Solis Rethinks Concealable Duty
What if Level I retention didn’t require a full duty rig? Safariland’s Solis delivers trusted ALS security in a streamlined OWB platform built for administrative and plainclothes professionals who need protection without the bulk.
Read More →
5 Things to Know When Buying Backup Lights for Patrol Use
What is the value of a backup light, and what do you need to consider when selecting one? These smaller lights are invaluable as a secondary or special-purpose light and can be easily carried in a pocket or clipped to MOLLE gear, a key chain, shirt, or a vest.
Read More →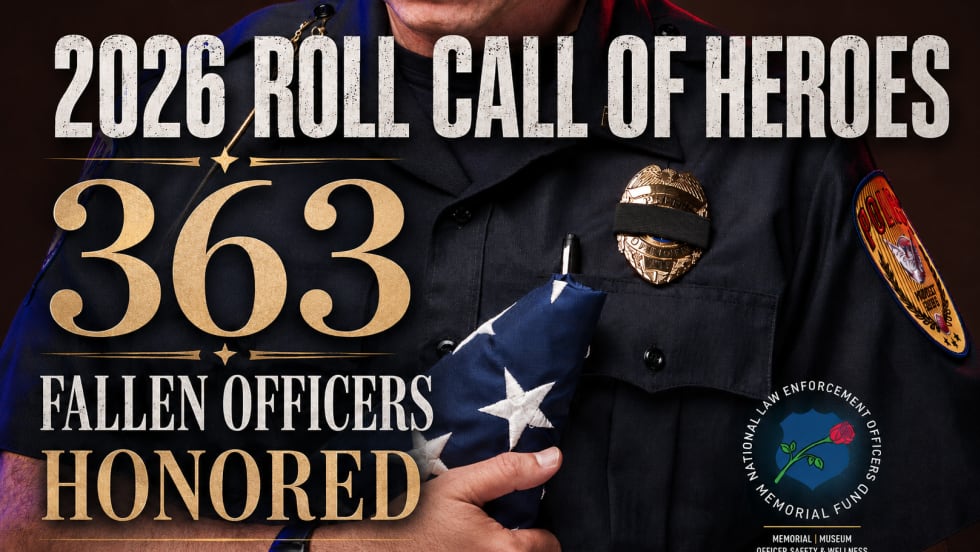
363 Fallen Officers Honored During National Police Week
In case you missed NELOMF’s annual Candlelight Vigil, here are all 363 names of the fallen officers whose names were added to the National Law Enforcement Officers Memorial this year.
Read More →
NYPD Officers Who Responded Quickly During IED Incident Recognized as NLEOMF Officers of the Month
Chief Aaron Edwards and Sgt. Luis Navarro were recognized by NLEOMF as Officers of the Month for their response during an IED incident and their actions that helped prevent harm to the public.
Read More →
National Police Survey Reveals How Americans View Policing Today
A new national survey offers a comprehensive look at how Americans view policing. The study uncovers public sentiment toward local vs. federal police, communications, crisis response, the use of AI in policing, and more.
Read More →
Streamlight TLR-7 X Selected as Standard Issue Pistol Light by Canadian Federal Police
The Canadian Federal Police will be adding a new duty pistol system, which will include Streamlight’s TLR-7 X and a Glock 45 MOS 7 pistol with a red dot sight.
Read More →
Fallen Law Enforcement Officers from Across the Country to be Honored During 38th Annual Candlelight Vigil on May 13th in Washington, D.C.
The National Law Enforcement Officers Memorial Fund (NLEOMF) will honor 363 fallen officers who have died in the line of duty as their names are added to the National Law Enforcement Officers Memorial during the annual Candlelight Vigil on May 13.
Read More →
What Should Be in Your IFAK?
What should every officer include in an IFAK? Sydney Vail, M.D., a veteran trauma surgeon and former SWAT surgeon, explains which components are needed and which are not, and stresses training.
Read More →


