
Now you can ask an expert your questions about facial recognition and read responses to others' questions on PoliceMag.com.
Read More →
Vigilant Solutions announced today that the Sacramento County (CA) Sheriff's Department is expanding the use of its FaceSearch facial recognition solution to approximately 500 agency users based on its success over the past year in a pilot operation.
Read More →
Face Forensics has significantly extended its f2 advanced face recognition technology by adding the capability to match images of tattoos against databases containing them.
Read More →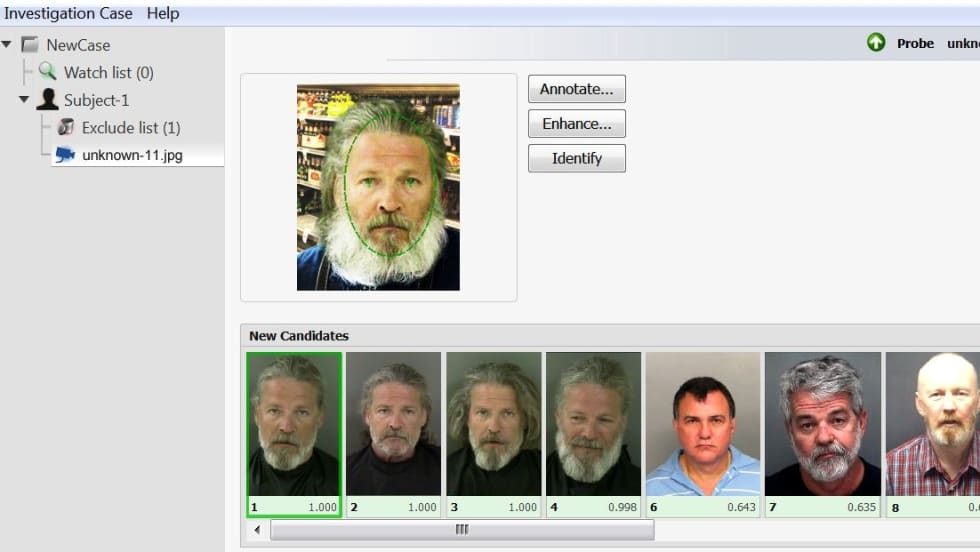
FaceVACS-DBScan compares facial images from different sources to multi-million-image databases and instantly creates a match list of the most similar faces.
Read More →
States increasingly are foiling crooks and scam artists by employing facial recognition software. The software uses algorithms of facial characteristics to compare driver's license or ID photos with other DMV images on file.
Read More →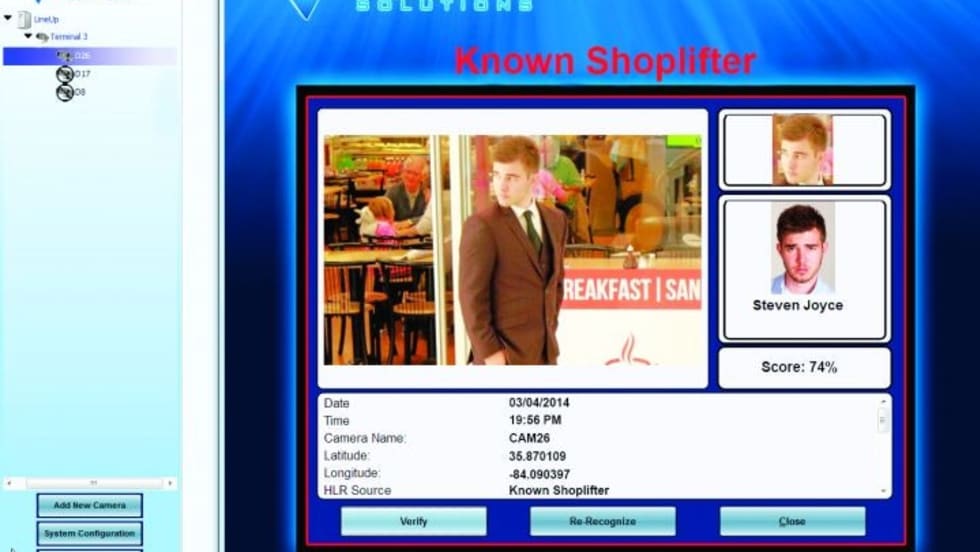
Imagine you are working a rape case and you're trying to identify the perpetrator. He posted a video of the crime and a profile picture of himself on online. You can use the image to search for the individual via Vigilant Solutions' FaceSearch facial recognition software.
Read More →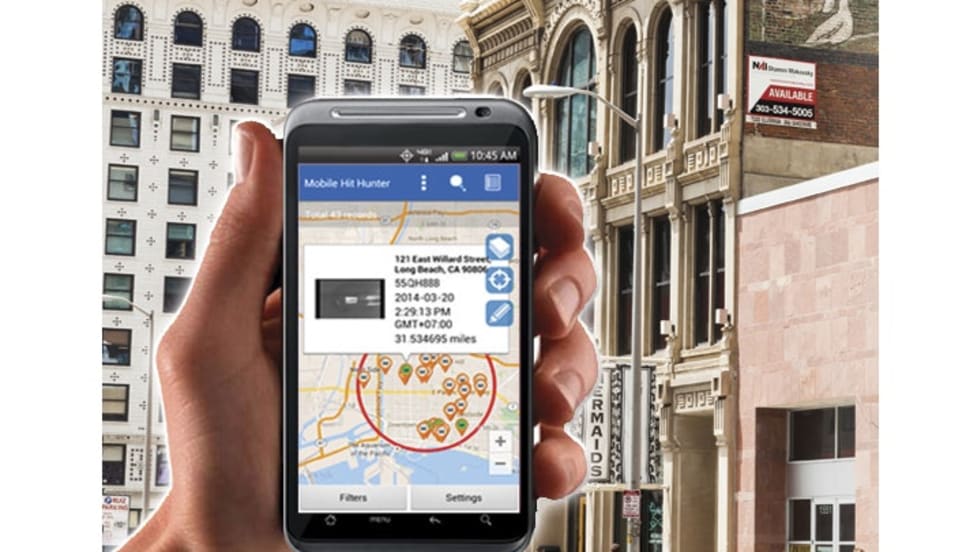
Vigilant Solutions' new Mobile Companion app leverages many of the new analytic tools that Vigilant has released in its LEARN product. These analytic tools are made even easier to use and more accessible on a mobile device.
Read More →
The FBI announced this week the achievement of full operational capability of the Next Generation Identification (NGI) System. It was developed to replace IAFIS and add new capabilities, including facial recognition.
Read More →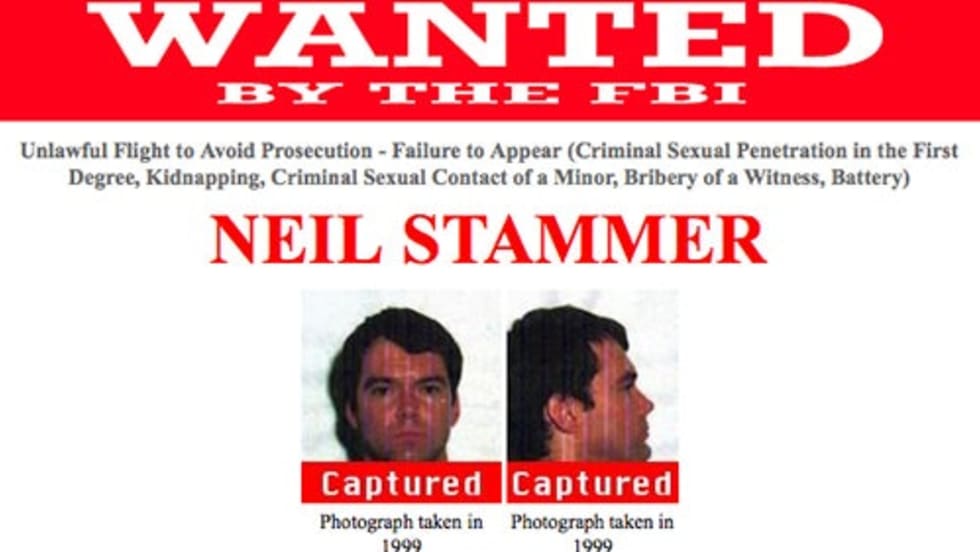
A U.S. fugitive on the lam for 14 years in connection with child sex abuse and kidnapping charges was apprehended in Nepal after authorities scanned his "wanted" poster with facial recognition technology.
Read More →
Computer security is one of the primary concerns for many of the nation's companies and government agencies. Billions of dollars is spent each year on preventing external threats from entering protected networks. But the sad truth is that most computer network breaches are caused by sloppy internal security policies and procedures.
Read More →