NIST Drafts Guide for Checking Apps Used at Work
The National Institute of Standards and Technology is readying guidance to help agencies evaluate commercial mobile applications that agency workers might use on government-issued devices or personal apps that access government networks.
The National Institute of Standards and Technology is readying guidance to help agencies evaluate commercial mobile applications that agency workers might use on government-issued devices or personal apps that access government networks, reports GCN.
The guidelines, Technical Considerations for Vetting 3rd Party Mobile Applications, currently in draft form, aim to help agencies assess a mobile app's security, behavior and reliability (including performance) so that they can determine if the app is acceptable for their environments.
The idea is that rather than being prescriptive, the guide is instructive, letting government officials choose what risks and tests apply to their agencies, said Tom Karygiannis, a NIST computer scientist. "There needs to be more awareness of what the apps actually do, what information they're collecting and how you may put your network at risk," Karygiannis said.
The guide is not a technical manifesto. "It's more of an education for end users who're not part of the IT department," Karygiannis added. "They need to have an awareness of how their security and privacy might be compromised as they use these devices."
Primary examples of things to test, according to the draft, include whether the app protects sensitive data and privacy, is reliable and available, and performs as promised.
More Technology

Safariland Solis Rethinks Concealable Duty
What if Level I retention didn’t require a full duty rig? Safariland’s Solis delivers trusted ALS security in a streamlined OWB platform built for administrative and plainclothes professionals who need protection without the bulk.
Read More →
How Patrolfinder Uses Data to Make Streets Safer
Law enforcement agencies have long relied on instinct and routine to optimize patrols. Patrolfinder uses data to help agencies see where officers go — and where they don’t — to improve visibility and maximize coverage.
Read More →
Crime Prevention by Merging Tech with Human Intervention
Elite Interactive Solutions tackles crime prevention with technology and human intervention, working closely with local police to provide insights when a response is needed. The key is to blend the latest in remote video monitoring, artificial intelligence, and a well-trained agent with eyes on the scene.
Read More →
Case Study Details Integration of Body-Worn Cameras with CAD
The Billerica Police Department (Massachusetts) improved transparency and accountability, sharpened evidence management, and reduced manual hours by integrating Axis Communications body-worn cameras with its Computer-Aided Dispatch (CAD) system.
Read More →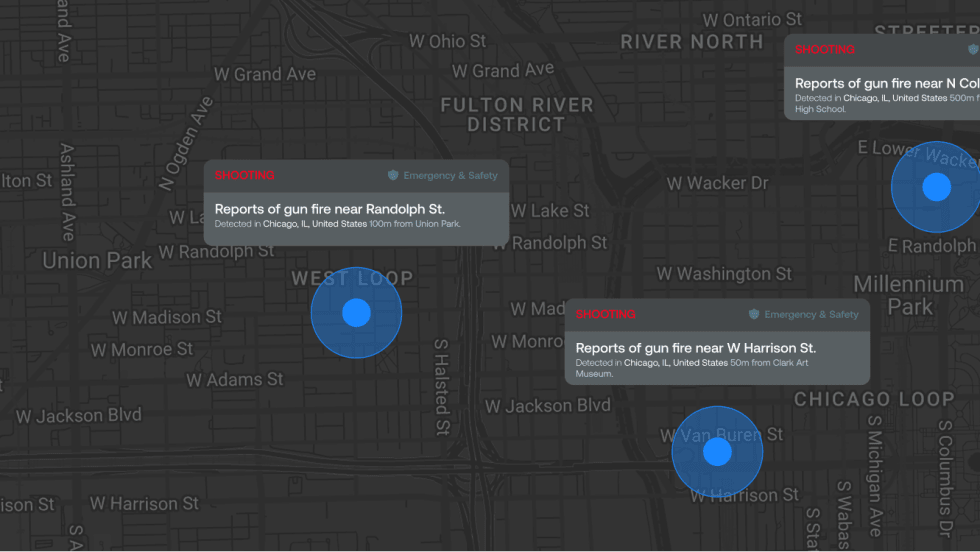
ZeroEyes Public Safety Alerts Integrates Samdesk for Real-Time Risk Detection and Awareness
ZeroEyes has integrated Samdesk into its Public Safety Alerts platform to deliver faster, verified intelligence to help organizations understand emerging risks and respond quickly.
Read More →
NJ Police Department Combines Strong Technology & Public Safety Strategy
The Fort Lee Police Department in New Jersey has modernized with Genetec Security Center, including video management, automatic license plate recognition (ALPR), and Clearance digital evidence management.
Read More →
Pimloc & Dynamic Workflow Solutions Partner to Deliver Data Management and Automated Redaction
The joint redaction solution from Pimloc and Dynamic Workflow Solutions helps agencies reduce FOIA response time and compliance risk by automatically redacting faces, license plates, and other sensitive information from digital evidence.
Read More →
The University of Alabama Rolls Out Couter-Drone Technology
The University of Alabama is using D-Fend Solutions as a counter-drone technology supplier for campus and game-day airspace security. The University integrates D-Fend’s EnforceAir into its Emergency Operations Center (EOC), utilizing a unified command framework to collaborate with local, state, and federal partners during major events.
Read More →
Motorola Solutions Now Part of the Cyber Threat Alliance
Motorola Solutions is now part of the Cyber Threat Alliance, the first formally organized nonprofit group of cybersecurity practitioners that work together in good faith to share threat information and improve global defenses against advanced cyber adversaries.
Read More →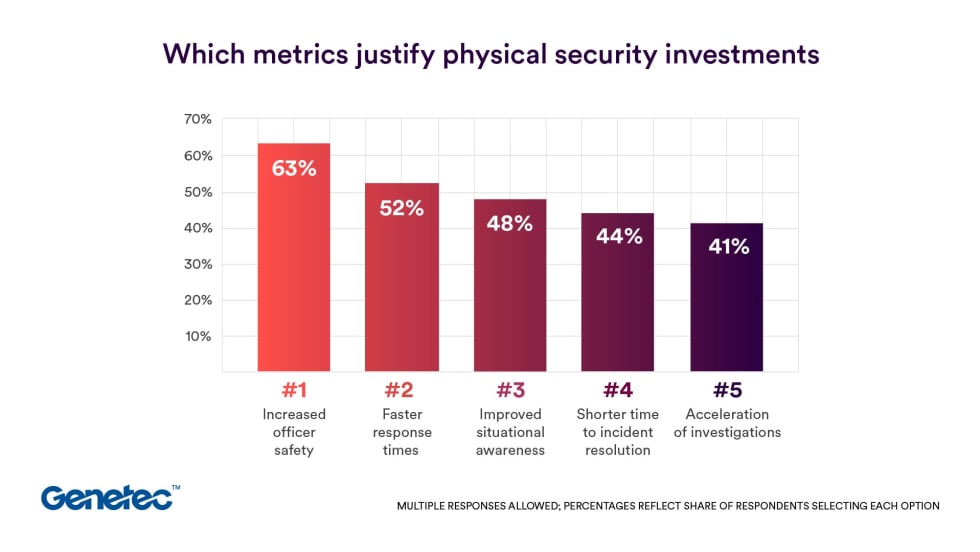
Genetec 2026 State of Physical Security Report Reveals Public Safety Priorities & Challenges
Survey results from Genetec’s 2026 State of Physical Security Report highlight the demand for integrated systems that improve response times and reduce investigative workload. Nearly nine in 10 respondents said they use security data to help keep officers safe.
Read More →


