Digital Ally has released new software updates for its local VuVault platform. Newly added features are designed to make it easier for you to manage your evidence and stay current with the latest technology.
MircoVuHD In-Car Video System
Digital Ally has released new software updates for its local VuVault platform. Newly added features are designed to make it easier for you to manage your evidence and stay current with the latest technology.
Digital Ally has released new software updates for its local VuVault platform. Newly added features are designed to make it easier for you to manage your evidence and stay current with the latest technology.
MircoVuHD In-Car Video System
You now have the availability to configure settings for the MicroVuHD In-Car Video System. This system uses RFID technology for the login process. With this release of VuVault, you also have the ability to program your agency's RFID cards for your MicroVuHD users.
VuVaultGO Mobile Software
Digital Ally has added support for the VuVaultGO mobile software application. The app allows for full system control including the ability to view the video feed, add notes, and play back recorded videos.
Other updates include:
DVM-800
Added Vehicle Speed Sensor settings for DVM-800
Removed the following settings:
Display Timeout
Triggered Record Time
Manual Record Time
Authorized Upload Times
Other
Added Auto Delete by Trigger options in the Auto Delete Policy under VuVault Settings
Moved some settings from the "Admin" pane to tabs in the new "Admin>VuVault Settings" menu
Moved global and individual device settings from "Admin>Settings" to "Admin>Devices"

The University of Alabama is using D-Fend Solutions as a counter-drone technology supplier for campus and game-day airspace security. The University integrates D-Fend’s EnforceAir into its Emergency Operations Center (EOC), utilizing a unified command framework to collaborate with local, state, and federal partners during major events.
Read More →
Motorola Solutions is now part of the Cyber Threat Alliance, the first formally organized nonprofit group of cybersecurity practitioners that work together in good faith to share threat information and improve global defenses against advanced cyber adversaries.
Read More →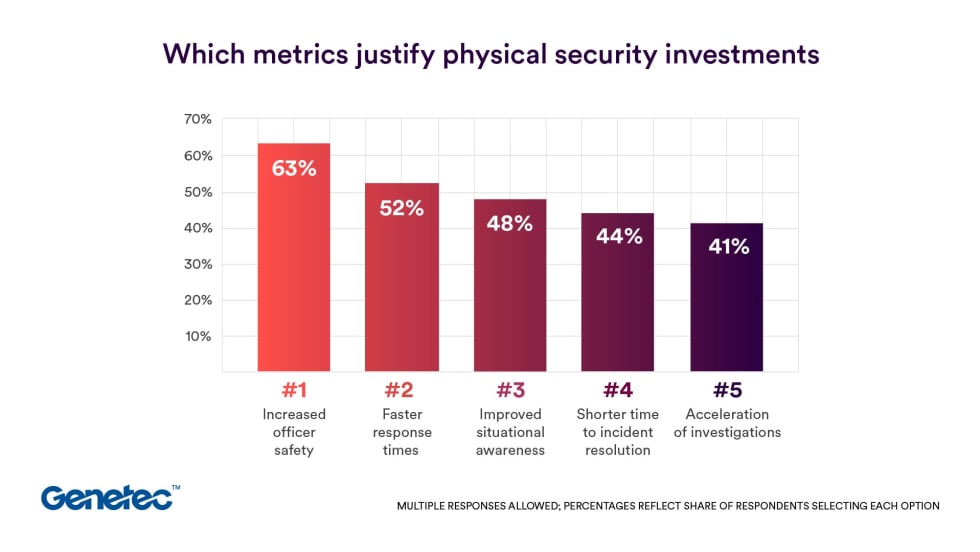
Survey results from Genetec’s 2026 State of Physical Security Report highlight the demand for integrated systems that improve response times and reduce investigative workload. Nearly nine in 10 respondents said they use security data to help keep officers safe.
Read More →
Audit Assistance is the latest tool in the Flock Trust & Compliance suite, a first-of-its-kind set of products and services that provides communities with guardrails and customization for accountability, transparency, and responsible use of the Flock platform.
Read More →
The Toughbook 56, the latest rugged laptop from Panasonic Connect, delivers enhanced performance, refined design, new levels of security, and power-efficient workflows in demanding environments.
Read More →
Radarsign’s traffic safety portfolio, including radar speed signs, flashing beacon systems, and more, are now available through Sourcewell purchasing contracts.
Read More →
D-Fend Solutions deployed its EnforceAir C-UAS system in support of local police to help secure a 19,000-attendee event, leveraging its non-jamming approach to keep communications and authorized drones operational while safeguarding against rogue drone threats.
Read More →
With World Cloud Security Day on April 3, Genetec outlines how enterprises can strengthen resilience as they modernize physical security in the cloud.
Read More →
Today’s police departments face rising fleet costs and must stay ready to respond, no matter the call. In this eBook, get powerful insights to enhance your police fleet’s cost-efficiency, reliability and performance through data-driven tactics.
Read More →
ALPR solutions provider Leonardo explains why leveraging technology for safety must never come at the expense of constitutional rights or community trust. Every action within an ALPR system should be logged in a tamper-proof audit trail with query records of who accessed what data, when, and for what purpose.
Read More →