Taking action against flying drones can lead to major repercussions even for law enforcement officers.
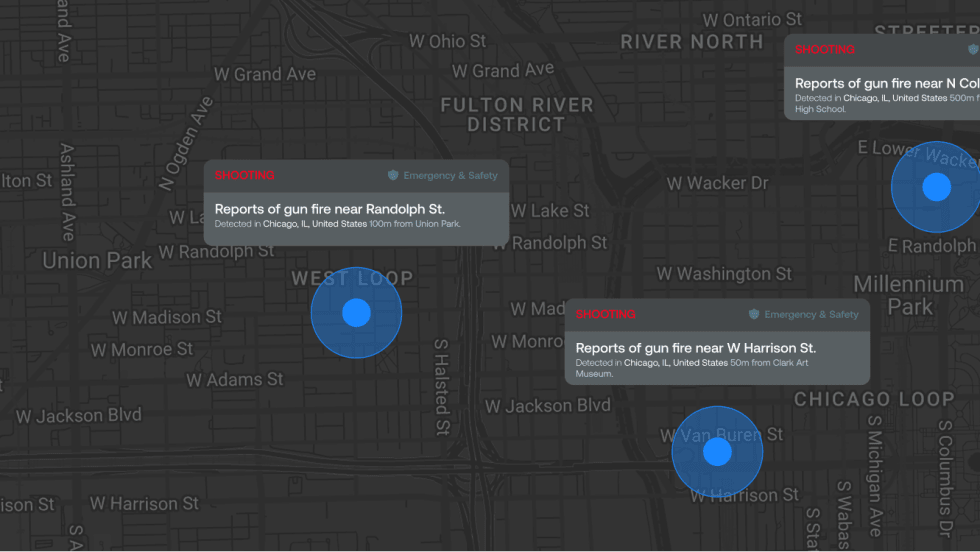
Within the law enforcement community, there has been significant concern about the growing use of drones for nefarious activities. The Internet is full of examples of the use of uncrewed aircraft systems (UAS) being used to drop contraband into prisons, transport drugs into the United States from Mexico, interfere with airport operations, attempt to disrupt critical infrastructure, or interfere with professional sports league events. In the Middle East and in Ukraine, we have also seen that small hobbyist drones can be used to carry bombs.
So it is of no surprise that state, local, tribal, and territorial law enforcement and public safety agencies as well as private entities are concerned about this evolving threat. They are seeking tools to protect their communities, facilities, and events.
In response to this threat, many law enforcement agencies have begun acquiring counter-UAS technologies. Some technologies such as drone gun jammers and some radio frequency detection technologies violate federal laws and regulations.
Restricted Response
Currently, there are significant limitations in the United States on which agencies can legally use certain counter-UAS systems. Congress has only authorized the Departments of Defense, Energy, Justice, and Homeland Security to conduct strictly regulated UAS detection and mitigation activities. Those activities are limited to UAS that are assessed as a credible threat to covered facilities or assets, notwithstanding federal criminal or surveillance laws that may apply. The Federal Aviation Administration (FAA) also has authority to engage in controlled counter-UAS detection and mitigation testing.
The limitations of counter-UAS technology are in place for several reasons, which include:
• UAS or drones, according to 49 U.S.C. § 44801(11), are considered aircraft.
• A UAS could meet the definition of a “protected computer” per the Computer Fraud and Abuse Act (CFAA).
• Some UAS may navigate through the airspace or communicate using signals from a satellite.
• Some UAS may navigate through the airspace or communicate through radio frequency signals.
• Some technical tools, systems and capabilities used to detect and/or mitigate UAS may violate federal laws and regulations.
• The use of certain Counter-UAS systems may impact the public’s privacy, civil rights, and civil liberties.
• Some Counter-UAS systems may impact the safety of the National Airspace System
Criminal Prosecution
Not only can taking action against a flying UAS be a violation of federal law, it can lead to criminal prosecution, even of law enforcement officers acting in the interest of public safety.
There are several federal criminal statutes that could be applicable regarding the use of certain detection and mitigation technologies. Examples include:
• The Aircraft Sabotage Act and the Aircraft Piracy Act may apply to actions taken to damage, disable, destroy, seize, or exercise control over a UAS, which is considered an aircraft. This could include jamming, spoofing, and cyber-takeover technologies as well as kinetic solutions such as nets and projectiles.
• The Pen/Trap Statute and the Wiretap Act may apply to radio frequency detection capabilities, whether in whole or in part, that capture, record, decode, or intercept electronic communications.
• The CFAA prohibits intentionally accessing a protected computer without authorization. The CFAA includes obtaining information, intentionally damaging a protected computer without authorization, and transmitting a program, information code, or command that causes damage.
• Interference with the operation of a satellite includes the obstruction or interference of satellite transmissions. A system that jams, spoofs, degrades, or interferes with GPS signals to or from a UAS or ground control station to a satellite may implicate this statute.
• Interference with communications related to military, law enforcement or public safety, or emergency personnel engaged in civil defense functions. A system that jams, degrades, or interferes with those types of communications may violate this statute.
FAA and FCC Regs
Federal criminal laws are not the only considerations to consider regarding the acquisition, installation, testing, and operation of UAS detection and mitigation systems. Both the FAA and the Federal Communications Commission (FCC) administer various laws and regulations related to aviation activities and the RF spectrum.
There are several laws that relate to the efficiency of the national airspace and aviation safety. An example includes the Sovereignty and Use of Airspace (49 U.S. Code § 40103). This code is important as it establishes the right of the public to transit through the navigable national airspace without improper interference.
Any UAS detection or mitigation systems that emit radio frequency waves, including radar systems, must be evaluated for compliance with any laws and regulations administered by the FCC. Radars, for example, require a Radiolocation Service license from the FCC.
When it comes to systems that can jam radio frequency signals, including handheld drone jammers, there are U.S. codes regarding manufacturing, importing, shipping, selling or using devices that fail to comply with FCC regulations. Those devices include those that are designed to block, jam, or interfere with wireless communications.
Another important clarification for public safety and law enforcement agencies to consider- the legal prohibitions mentioned are not based on broad classifications of systems. Legal prohibitions are not based on whether the system detects drones or mitigates drones, nor is it based on whether the system emits or receives RF waves (active vs. passive). The legal prohibitions are based on the functionality of each individual system and the specific methods in which the system is used and operated.
What You Can Do
Despite the limitations we've discussed, there are steps that can be taken now to begin to prepare your department or agency for the three-dimensional threat presented by drones. These steps can be accomplished with the assistance of companies and personnel with relevant homeland and law enforcement counter-UAS knowledge and experience.
• Training—Training includes understanding UAS threats, UAS fundamentals, UAS rules and regulations, and basic Counter-UAS operations, to name a few.
• Policies and Procedures—Developing policies will provide general guidelines that outline your organization’s play for tackling airspace awareness and security issues. Developing procedures will provide a blueprint for how to deal with specific situations.
• Technology—There are technical solutions available that do not violate federal laws and regulations. Radar, acoustic, and EO/IR cameras are less likely to violate federal criminal surveillance statutes. RF detection systems should be evaluated based on functionality to see if follow recommendations. Mitigation systems meant to disable, disrupt, or destroy drones will violate federal laws and regulations.
Any agency seeking to add counter-UAS solutions should strongly consider the following recommendations:
• Seek advice from counsel experienced with federal, state, and local criminal surveillance and communications laws.
• Evaluate whether the functionality or use of any UAS detection or mitigation systems impact the public’s privacy, civil rights, and civil liberties.
• Conduct your own legal and technical analysis of the systems functionality and legality.
• Do not rely on the representations of vendors or consultants on the legality or functionality of the systems.
• Thoroughly evaluate the homeland/urban/public safety Counter-UAS knowledge and operational expertise of vendors and consultants.
• There are no counter-UAS authorities or provisions for state, county, municipal, tribal agencies that have officers assigned to federal task forces,such as the FBI’s Joint Terrorism Task Force (JTTF).
The airspace awareness and security challenges involved in drone response are complicated and evolve very quickly with the pace of technology and tactics used by nefarious actors. The counter-UAS legislative authorities that many law enforcement agencies have been waiting for have not yet materialized. So agencies should use caution when evaluating and purchasing counter-UAS technologies, and take logical steps in the meantime to begin developing their programs within the established legal and regulatory boundaries.
This article is provided for informational purposes only and is not intended as and should not be relied upon or construed as a legal opinion or legal advice regarding any specific issue or factual circumstance.
Tom Adams is CEO of AeroVigilance and Co-Founder of C-UAS Hub. He served 20 years with the FBI in a variety of operations, including counter-terrorism. His last three years with the FBI, he served as supervisory special agent in the Counter-UAS Program.