Spy Gear
Since September 11, 2001, the development of new electronic surveillance techniques and equipment has been in overdrive.
Since September 11, 2001, the development of new electronic surveillance techniques and equipment has been in overdrive. Fueled by a national desire to make our homeland safe for our citizens, the surveillance industry has sprung to life to supply law enforcement agencies with an almost endless array of electronic gadgets.
Whether it's for watching, listening, tracking, documenting, or recording, there's someone who can build it if you'll buy it. But before you go out and start spending all those dollars, do your due diligence.
Technology has taken huge leaps over the last few years, and it's important to make sure you're getting the right equipment for the task at hand. Remember, surveillance equipment used under the proper circumstances can be a force multiplier. Used inappropriately, however, you'll find yourself and your department bogged down in endless litigation as the privacy laws are in a tremendous state of flux and our friends at the ACLU are worried about everyone's civil liberties.
Learning the Lingo
Before you go off and start ordering equipment you need a basic understanding of the technology behind it.
The first technology issue to be aware of is analog vs. digital signals. A few years ago this wasn't an issue. Today it can make a huge difference in what you are attempting to accomplish. An analog signal is continuously variable, while a digital signal consists of discrete states, the exact opposite.
A digital signal is a binary signal, which means it has only two states, 0 and 1. Think back to when you were a kid and your parents had a television antenna on the roof. Sometimes you got a picture and sometimes you saw a blizzard of snow on the screen, or a continuously variable signal. Today's high definition TV is digital; the picture is there or it's not. There's no fine-tuning knob to fool with to get a better picture. This same premise applies not only to video signals, but to audio as well.
Next is encryption. It's been part of the cloak-and-dagger world for years, developed out of necessity for national governments. But until recently it wasn't readily available to local law enforcement. Today, your department better understand encryption and use it often or all your hush-hush investigations will end up on the local evening newscast before you have a chance to send them to your local prosecuting attorney.
Encryption, or cryptography, is the science of writing secret codes and has been used to protect the security of communications for hundreds of years. Essentially, cryptography enables the encoding of information so that only the intended recipient has the ability to understand its meaning. Today, it's the best way to protect the privacy and security of electronically transmitted information.
There are other matters to consider when deciding what electronic surveillance products to buy. Size and form, power consumption of the device, transmission power, and wireless vs. wired technology are just a few of the factors that will greatly influence your purchasing decisions.
Wired Vs. Wireless
Over the past few years, wireless technologies have leaped beyond every expectation. While this speedy progress is great, it's also part of the problem. Advancements are coming so fast that a platform you buy today may be obsolete by next year.
Just look at the wireless 802.11 standards. First it was "b," now it's "g," and soon it will be "n." Each letter change marks the ability for data to move more quickly. At first it was 5, then 54, and then 100 megabytes from point to point. Other vendors decided they would use the FCC license-free 2.4-GHz spread spectrum equipment. The problems you'll run into using this band are that anyone can use it, you are limited in your transmission power, and you won't find a lot of compatible encryption equipment.
An alternative to the 2.4-GHz spread spectrum is cellular video surveillance. In January 2003 I used this technology provided by VivaMicro, a San Diego company, to increase law enforcement presence while remotely managing one of the events associated with the Super Bowl. This secure path allowed department managers to make decisions about manpower allocations without having to go to the scene. The company's technology has also been used to send digital still pictures to a secure Website to catch "taggers" in the act, leading to successful prosecutions.
Secure Internet Based
Another form of video surveillance is wired or IP based. This type of surveillance is usually set up in plain sight but can be easily disguised for covert operations.
One provider of this type of technology is Dotworkz Systems. When faced with an ever growing amount of violence at some of San Diego's more popular beach venues on the Fourth of July weekend, SDPD approached Dotworkz because the company already had two Web-based, pan-tilt-zoom "dome cameras" located at two of our potential flashpoints. One of the two sites is also known for its narcotics activity.
By working with the company we gained exclusive access to the cameras during the holiday weekend. These cameras have powerful zoom lenses that allowed us to see a half-mile up and down the beach boardwalk. Each camera is also equipped with an automatic iris and works wells in low-light situations. By gaining access to this public asset, our decision makers were able to see and evaluate first person information without any translation or embellishment.
FCC Licensed
Another type of video surveillance is wireless aerial, which typically uses cameras mounted on a helicopter or fixed-wing aircraft. In most cases these are licensed by the FCC and operate between 2200 and 2500 MHz. But many network and local television news helicopters also operate on this frequency, so beware. If it's in the air and not encrypted you may find the local news is broadcasting your SWAT tactical video as you're trying to set up your perimeter.
One of the leaders of the new digital video systems technology is a joint venture between Pacific Microwave Research of Vista, Calif., and the Center for Commercialization of Advanced Technologies. PMR is developing a state-of-the-art digital video incident management tool to enhance its analog tactical video receiver (TVR), a handheld unit that displays video imagery transmitted by aerial assets or frontline surveillance platforms working within the shared spectrum.[PAGEBREAK]
A New Band
Help is on the way. The Federal Communication Commission (FCC) has recently allocated the 4940-4990 MHz band (4.9 GHz band) for fixed and mobile wireless services and has designated the band for use in support of public safety.
This allocation provides public safety users with an additional spectrum to support new broadband applications such as high-speed digital technologies and wireless local area networks for incident scene management. The spectrum also can support dispatch operations and vehicular or personal communications.
Concealed Devices
In the mid-1970s, charge-coupled devices (CCDs) or solid-state video cameras were developed at Bell Labs. Because of miniaturization, these devices are becoming more efficient and useful for a variety of tasks.
The next generation of Complementary Metal Oxide Semiconductors (CMOS) will be less expensive and ultimately do more. Soon police surveillance will be just like a James Bond movie. Video cameras have become so small that they can be easily concealed in ball caps, tie clips, and fountain pens. It won't be too long until the latest trend of still cameras in cell phones becomes passé.
Unfortunately, there generally is a trade off. To achieve a smaller size you need to give up either power or flexibility, especially in the area of lens technology...But now that's changing.
Vision Technology, based in Rogers, Ark., has developed digital cameras that are equipped with specially designed, compact, indefinite focus lenses. The indefinite focus lens is designed to achieve the greatest depth of field possible, with no edge distortion. The lenses are sized to efficiently cover their CCD imagers.
Vision Technology's patented indefinite focus lens provides simultaneous focus from one-quarter inch to infinity. This gives you superior depth of field. The indefinite focus lens eliminates the need to focus on specific targets, whether the target is near or far from the user, and it's accomplished with no moving parts or software manipulation.
Audio Surveillance
They say a picture is worth a thousand words, but sometimes you need someone's voice on tape. And most suspects aren't willingly going to let you record their voices. That's where audio surveillance comes in.
One of the more interesting ways of listening to others without their knowledge is to use one of the so-called "ghost phones." It's an ordinary cellular phone with a difference: When the phone appears to be switched off or non-functional, it's acting as a fully operational sensitive audio device. The phone's modified circuitry and software are used to transmit any sounds the phone can pick up, using the lines of a local phone company anywhere in the world.
Who needs "bugs" that only transmit a few hundred feet when you can get one of the nationwide carriers to provide free long distance surveillance? Well, it's not necessarily that simple. You need to be careful here. There are a number of state, federal, and more than likely local violations associated with the exploitation of telecommunications companies.
Speaking of bugs, there are a ton out there, but your major concerns once again will be power consumption and range of transmission. Both are a component of size, but useful range will be affected by environmental factors such as terrain and structure. The rule in most cases: line of sight. Whether you're operating a bug on UHF, VHF, or 2.4 GHz you're always going to get the best signal using a directional antenna to send and receive the signal.
Letter of the Law
Now before you go out and drop a dumptruck full of cash on some new whiz-bang technology that promises to do everything for you but handcuff the suspect, don't forget to look into the laws that control the uses of such technologies.
Remember, terrorists or not, we still live in a free society. Just because the Patriot Act has loosened the rules for the Federal Government, your local jurisdiction still needs to be aware of, and obey, local or state regulations when conducting surveillance. Finding the balancing point between legal electronic surveillance and an individual's right to privacy will be something our nation's courts will tackle in the future. Be smart, exploit the technology for all it's worth, but use integrity in your professional conduct.
Bob Davis is a 27-year veteran of the San Diego Police Department who has been responsible for the technical security of events such as the 1996 Republican National Convention, two Super Bowls, the 2001 BioTech convention, and other incidents or events within the city of San Diego. He currently runs SDPD's computer lab.
More Technology

Safariland Solis Rethinks Concealable Duty
What if Level I retention didn’t require a full duty rig? Safariland’s Solis delivers trusted ALS security in a streamlined OWB platform built for administrative and plainclothes professionals who need protection without the bulk.
Read More →
How Patrolfinder Uses Data to Make Streets Safer
Law enforcement agencies have long relied on instinct and routine to optimize patrols. Patrolfinder uses data to help agencies see where officers go — and where they don’t — to improve visibility and maximize coverage.
Read More →
Crime Prevention by Merging Tech with Human Intervention
Elite Interactive Solutions tackles crime prevention with technology and human intervention, working closely with local police to provide insights when a response is needed. The key is to blend the latest in remote video monitoring, artificial intelligence, and a well-trained agent with eyes on the scene.
Read More →
Case Study Details Integration of Body-Worn Cameras with CAD
The Billerica Police Department (Massachusetts) improved transparency and accountability, sharpened evidence management, and reduced manual hours by integrating Axis Communications body-worn cameras with its Computer-Aided Dispatch (CAD) system.
Read More →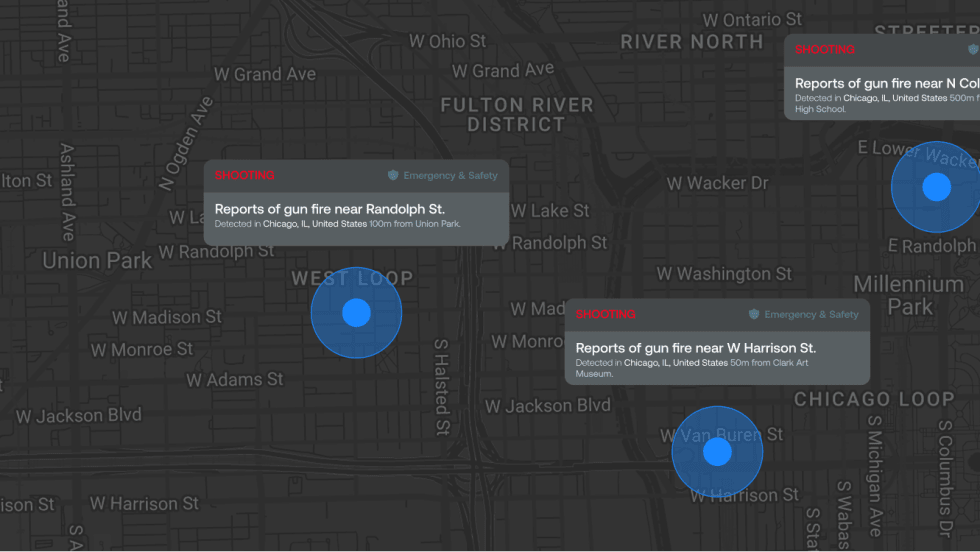
ZeroEyes Public Safety Alerts Integrates Samdesk for Real-Time Risk Detection and Awareness
ZeroEyes has integrated Samdesk into its Public Safety Alerts platform to deliver faster, verified intelligence to help organizations understand emerging risks and respond quickly.
Read More →
NJ Police Department Combines Strong Technology & Public Safety Strategy
The Fort Lee Police Department in New Jersey has modernized with Genetec Security Center, including video management, automatic license plate recognition (ALPR), and Clearance digital evidence management.
Read More →
Pimloc & Dynamic Workflow Solutions Partner to Deliver Data Management and Automated Redaction
The joint redaction solution from Pimloc and Dynamic Workflow Solutions helps agencies reduce FOIA response time and compliance risk by automatically redacting faces, license plates, and other sensitive information from digital evidence.
Read More →
The University of Alabama Rolls Out Couter-Drone Technology
The University of Alabama is using D-Fend Solutions as a counter-drone technology supplier for campus and game-day airspace security. The University integrates D-Fend’s EnforceAir into its Emergency Operations Center (EOC), utilizing a unified command framework to collaborate with local, state, and federal partners during major events.
Read More →
Motorola Solutions Now Part of the Cyber Threat Alliance
Motorola Solutions is now part of the Cyber Threat Alliance, the first formally organized nonprofit group of cybersecurity practitioners that work together in good faith to share threat information and improve global defenses against advanced cyber adversaries.
Read More →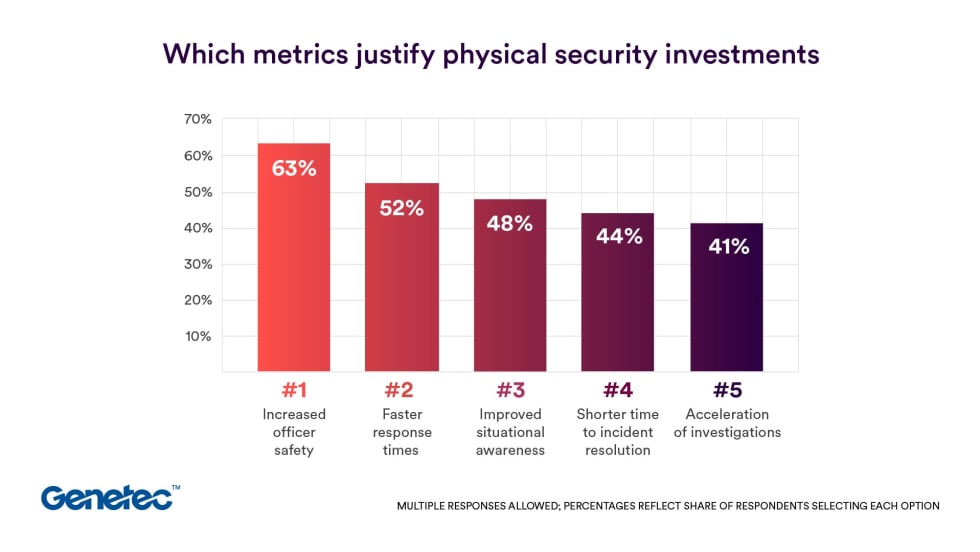
Genetec 2026 State of Physical Security Report Reveals Public Safety Priorities & Challenges
Survey results from Genetec’s 2026 State of Physical Security Report highlight the demand for integrated systems that improve response times and reduce investigative workload. Nearly nine in 10 respondents said they use security data to help keep officers safe.
Read More →


