Some elected officials seem compelled to introduce legislation aimed at protecting the rights of suspected criminals while impeding our investigations. On July 9, Rep. Edward Markey (D-Mass.) issued a press release alleging that law enforcement officers were abusing their authority and compromising the rights of innocent consumers by making excessive requests for cell phone data.
Markey derived his information from data he allegedly received from nine mobile wireless carriers. Markey declared that in 2011, "federal, state, and local law enforcement agencies made more than 1.3 million requests of wireless carriers for the cell phone records of consumers, and the number is increasing every year."
Lacking context, this comes across as an alarming statistic. But Markey neglected to mention that from 2010 to 2011, wireless communication transmissions increased by 123%.
Instead, Markey seeks to exploit an isolated statistic to suggest that law enforcement is engaging in an uncontrolled electronic fishing expedition. Does Markey really think we have the time or desire to recklessly request voluminous records irrespective of any specific investigative purpose?
Nonetheless, Markey attempts to validate his position by stating in his release, "We cannot allow privacy protections to be swept aside with the sweeping nature of these information requests, especially for innocent consumers. Law enforcement agencies are looking for a needle, but what are they doing with the haystack?"
Are we to infer that if a criminal pays his cell phone bill on time, he is an "innocent consumer?" Furthermore, suspected criminals should not be trivialized as "needles" in a misapplied analogy. We are not trampling on static straws of "hay," but are instead functioning in a fast-moving, dynamic environment. Law enforcement officers endure great risk and sacrifice pursuing terrorists, drug traffickers, fugitives, and violent gang members, while upholding the sacred due process of law.
Since Markey first alleged that law enforcement was violating the rights of innocent consumers, FLEOA recommended that he query the various internal affairs and inspector general units of our agencies to ascertain the number of substantiated cases of abuse. Markey opted not to pursue this reasonable course of action, but instead to rely exclusively on the isolated data that the carriers provided. Had he made the good faith effort we requested, he would have learned that there is no epidemic of law enforcement abuse.
Undeterred, Markey issued another press release on August 9, announcing the draft of his new legislation, The Wireless Surveillance Act of 2012. In the draft, he mischaracterizes legitimate law enforcement efforts to obtain cell phone records as a "startling number of requests."
Additionally, Markey's legislative proposal fails to recognize the rampant increase in identity theft and the harmful impact this crime has on "innocent consumers." Identity thieves rely on their access to wireless communications to accomplish their goals, and their mobility continues to pose a significant challenge to law enforcement. While Rep. Markey claims that his legislation would bring greater accountability, in effect it would only serve as a trip wire to disrupt law enforcement efforts to pursue criminals and their accomplices.
On May 17, FLEOA Vice President John Ramsey testified at a congressional hearing in opposition to H.R. 2168, the Geolocational Privacy and Surveillance Act. He represented federal law enforcement officers by opposing the implementation of further restrictions on law enforcement's ability to obtain wireless information. In his testimony, he posed an important question followed by poignant commentary: "Do we really want to slow down the apprehension of murderers and rapists so they can build their trophy wall by increasing the amount of legal documents necessary for law enforcement to gather information?"
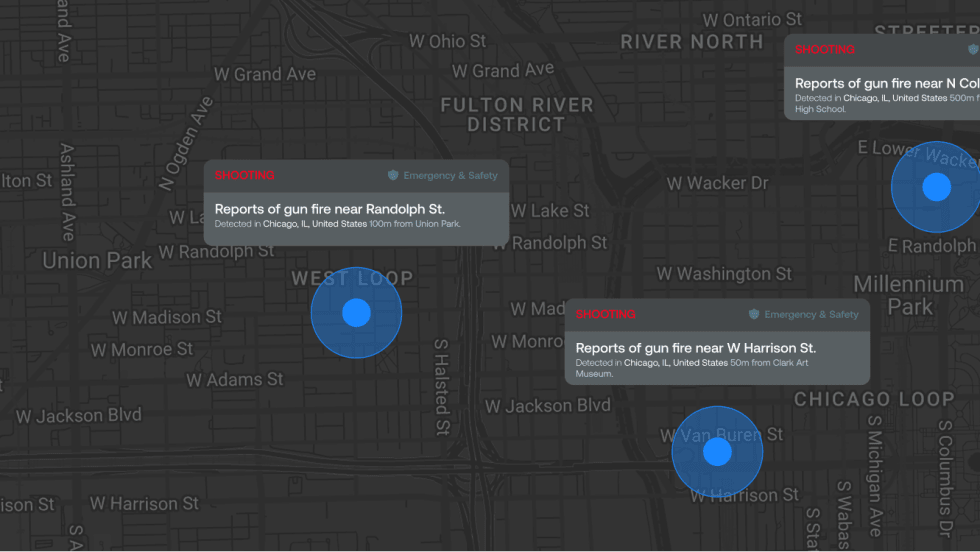
With the advent of e-mail, Twitter, voice over Internet protocol, Facebook, instant messaging, and other wireless media, criminals have more tools than ever to accomplish their objectives. Recognizing the value of wireless communication, numerous criminals have dropped their guns and picked up smart phones and tablets. As the number of wireless communication options grows, so will the number of criminals seeking to exploit them. If Markey would take pause to consider this, he might come to realize that his legislation serves to protect criminal conduct and not innocent Americans.
Related: