New Challenges in Cyber Forensics
Today's digital investigator must learn how to extract evidence from drones, encrypted portable devices, cryptocurrency trades, and a growing range of appliances and products defined as the Internet of Things (IoT).

Don't say the wake word to a Smart Speaker at a crime scene. If you do and the system hears it, you will destroy evidence. (Photo: Getty Images)
A little more than a decade ago the work of a digital forensic specialist was pretty much about computers. Then along came the iPhone and Android and the challenge of the spread of portable devices. Now new challenges are arising from technologies that few people even imagined before they burst upon the market. Today's digital investigator must learn how to extract evidence from drones, encrypted portable devices, cryptocurrency trades, and a growing range of appliances and products defined as the Internet of Things (IoT).

Drone piloting is one of the most popular hobbies in the United States, and these aircraft are now being used in crime. (Photo: Getty Images)
Flying Things
One of the most popular gifts found under the Christmas trees of average Americans the last two years were hobby drones. These small remote-controlled aircraft look like toys, but they are actually extremely sophisticated devices capable of capturing 4K-quality video, carrying payloads, and flying programmed routes well beyond line of sight. So it's little wonder that drones have caught the eyes of enterprising criminals, miscreants, and even terrorists.
The most common criminal activity involving drones is smuggling. These little birds can carry a few pounds of drugs or cellphones or other contraband into prisons. And they have been discovered doing so in the United States and in numerous foreign countries.
Drones can also carry drugs across the border. At least one such failed attempt was discovered south of the California border town of San Ysidro in 2015. Since then more crashed drones have been discovered. And only the unsuccessful ones make the news or fall into law enforcement hands.
The second most common category of drone crimes falls under the heading of harassment and surveillance. Drones are being used by stalkers and sex offenders to monitor their prey. They have also been used to spy on and even disrupt law enforcement operations. Drone pilots have even accidentally or intentionally buzzed and even struck police aircraft.
Weaponized hobby and commercial drones are also common in war zones. In Iraq terrorists have used drone swarms to carry out IED attacks. Last year in one of the most devastating drone attacks ever, pro-Russian separatists hit a huge Ukrainian military munitions storage facility with a single drone carrying a thermite grenade. The attack reportedly destroyed more than $1 billion in arms and ammunition. The size of the drone has not been reported, but the grenade did not have to be large, and there are numerous commercial and even hobby drones that could have done the job.
The growing use of drones in criminal activity means that law enforcement is recovering them at crime scenes. Some have crashed; some were intentionally brought down by officers.
Regardless of how a drone that was used in a crime falls into law enforcement hands, pulling evidence off of it will involve digital forensic analysis. But even officers and detectives at the scene need to know how to handle the device. No matter what the drone looks like, it is not a toy. Don't handle it without proper crime scene protocol because you might contaminate physical evidence left on the device by the perps. And don't turn it on because doing so might alter the digital evidence. Also, don't do what some agencies have done and auction off a drone as seized property without having it analyzed for evidence.
Drones are becoming such a concern for forensic investigators that three of the largest makers of cyber evidence analysis software, Cellebrite (www.cellebrite.com), MSAB (www.msab.com), and Oxygen Forensics (www.oxygen-forensic.com), recently demonstrated their new drone analytics tools at the Techno Security & Digital Forensics Conference held last month in Myrtle Beach, SC.
These new drone tools are being incorporated into the companies' flagship cyber forensics software products and can interpret data captured by drones, including flight path, altitude, and speed. They can also help analysts recover video and photos captured by the drone and metadata from any photos or video recovered.
Experts say the amount of evidence that can be pulled off of a drone is limited by what is actually captured by law enforcement. Most of the time, the drone is recovered but not the controller or the smart device used to operate it. And as for data stored in the cloud, that's a non-starter because the servers are in China or controlled by Chinese companies.
But there are at least two depositories of cyber evidence on the typical hobby drone: the camera memory and the internal memory. Cellebrite, MSAB, and Oxygen offer training to teach digital forensic specialists how to properly access and analyze this data.
Encoded Cash
One of the greatest challenges now facing law enforcement is the development of cryptocurrencies such as Bitcoin. It's estimated that 25% of all Bitcoin users are involved in some kind of criminal activity. This means that cryptocurrency evidence is becoming more common at crime scenes.
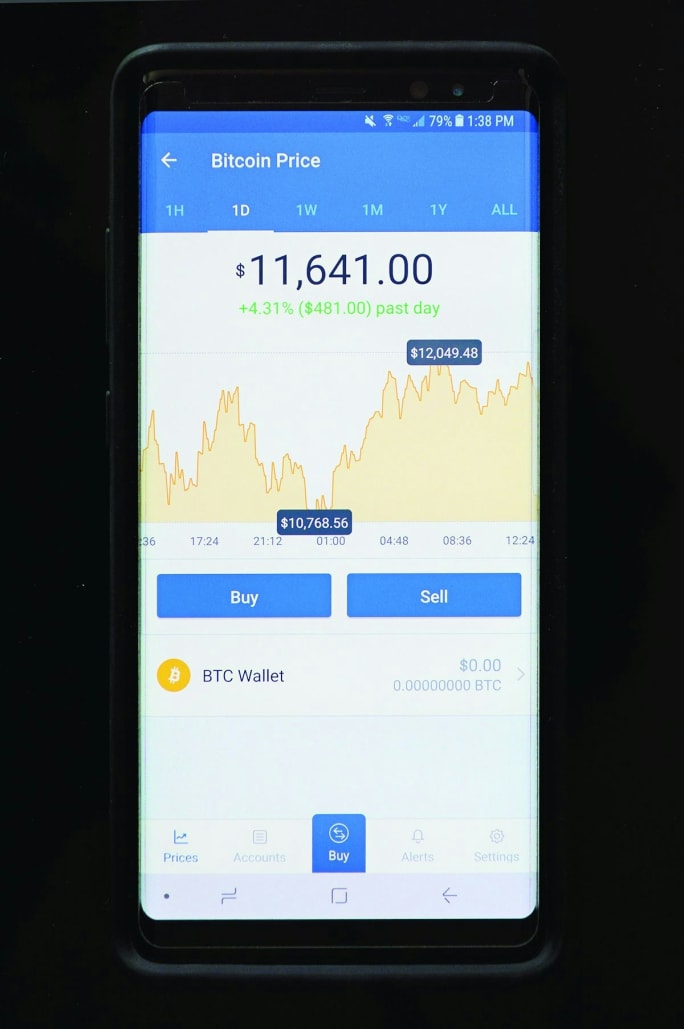
Example of a Bitcoin wallet. (Photo: Aaron Strain)
A cryptocurrency is an encrypted piece of code that can only be read by someone with the keys. It was recently estimated that there are 1,600 of these financial devices available. Only about four of them are really common: Bitcoin, Litecoin, Ethereum, and Monero. There's a reason why these coded currencies are so popular with crooks: They are pretty much untraceable unless you have the public and private keys. Which should be target number one of any investigation of criminal activity involving computers these days.
Let's say you are investigating a scene where someone perpetrated a ransomware attack. Don't think this unlikely. You don't have to be a computer genius to hit an organization or individual with ransomware. Kits for launching such attacks are available on the Dark Web and the bad guys can even hire someone to do it for them and just take a cut.
So back to our scenario; you are investigating the home or office of someone suspected of launching a ransomware attack. One of the primary targets of your search is the suspect's cryptocurrency "wallet." This wallet could be a piece of software on a device, it could be a thumb drive-looking piece of hardware, or it could be paper with a series of words or numbers on it, often as many as 16 different sequences or words.
Treat this scene as extremely fragile. Whatever you do, do not turn off any devices or disconnect the drives. Get the experts on scene to capture RAM memory (the memory that erases when the device is shut down).
Alexa, Record My Murder
WiFi technology in our homes and offices has enabled the development of a wide variety of appliances and devices that are connected to the Internet, including smart TVs, refrigerators that track consumption of foods and create shopping lists, and the smart speaker.
The smart speaker, most commonly the Amazon Echo with Alexa software or the Google Home, is by far the most popular device in the Internet of Things (IoT), which is the fastest growing category of digital devices on the market. It is estimated that by 2020, there will be more IoT devices in America than people.
Some homes and offices have more than one of these Amazon or Google devices. (The author has three.) These devices listen for their wake words and execute spoken commands such as telling time, setting alarms, playing online radio stations, and answering simple questions. With additional accessories, they can also manipulate thermostats, lighting, and other controls.
Smart speakers are showing up at more and more crime scenes. During a presentation at last month's Techno Security & Digital Forensics Conference four out of approximately 50 digital forensics analysts attending a presentation on IoT devices said they had dealt with smart speakers.
The presence of such devices at crime scenes means officers and analysts need to know how to handle them. The most important thing to know is what not to do. Don't say the wake word. If you do and the system hears it, you will destroy evidence. The system has very limited onboard memory. Saying the wake word erases one of its most recent commands.
Most of the data from smart speakers, however, is captured in the app on the owner's phone or tablet or on the cloud. These devices are not computers; they are portals to computers in the cloud that tell the Alexa or Home or whatever to execute your commands. That's why they are basically paperweights when they lose their WiFi connection.
The good news from an investigative standpoint is that everything ever asked of these devices is stored on the cloud until the user erases it from the app. The bad is that the cloud servers are controlled by huge companies that tend to ignore warrants or fight them. If you really need the command data from a smart speaker your best bet is to access it from the app on the owner's phone or tablet. And of course, the easiest way to do this is to get the victim, suspect, or other individual with legal standing to give you the user name and password.
That's exactly what happened in the most publicized instance of investigators seeking evidence from a smart speaker. Benton County, AR, prosecutors served Amazon with a warrant for the cloud data from a murder suspect's Alexa. Amazon fought the warrant, as it probably didn't want to set a precedent of handing over such data. After months of legal wrangling, no precedent was set. The suspect's attorney gave the prosecution the user name and password for the app.
More Technology

Safariland Solis Rethinks Concealable Duty
What if Level I retention didn’t require a full duty rig? Safariland’s Solis delivers trusted ALS security in a streamlined OWB platform built for administrative and plainclothes professionals who need protection without the bulk.
Read More →
How Patrolfinder Uses Data to Make Streets Safer
Law enforcement agencies have long relied on instinct and routine to optimize patrols. Patrolfinder uses data to help agencies see where officers go — and where they don’t — to improve visibility and maximize coverage.
Read More →
Crime Prevention by Merging Tech with Human Intervention
Elite Interactive Solutions tackles crime prevention with technology and human intervention, working closely with local police to provide insights when a response is needed. The key is to blend the latest in remote video monitoring, artificial intelligence, and a well-trained agent with eyes on the scene.
Read More →
Case Study Details Integration of Body-Worn Cameras with CAD
The Billerica Police Department (Massachusetts) improved transparency and accountability, sharpened evidence management, and reduced manual hours by integrating Axis Communications body-worn cameras with its Computer-Aided Dispatch (CAD) system.
Read More →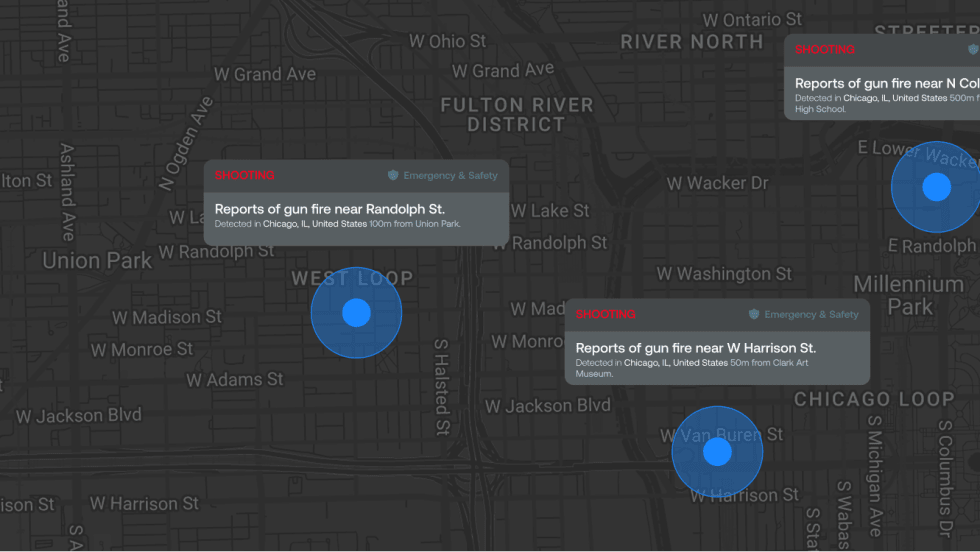
ZeroEyes Public Safety Alerts Integrates Samdesk for Real-Time Risk Detection and Awareness
ZeroEyes has integrated Samdesk into its Public Safety Alerts platform to deliver faster, verified intelligence to help organizations understand emerging risks and respond quickly.
Read More →
NJ Police Department Combines Strong Technology & Public Safety Strategy
The Fort Lee Police Department in New Jersey has modernized with Genetec Security Center, including video management, automatic license plate recognition (ALPR), and Clearance digital evidence management.
Read More →
Pimloc & Dynamic Workflow Solutions Partner to Deliver Data Management and Automated Redaction
The joint redaction solution from Pimloc and Dynamic Workflow Solutions helps agencies reduce FOIA response time and compliance risk by automatically redacting faces, license plates, and other sensitive information from digital evidence.
Read More →
The University of Alabama Rolls Out Couter-Drone Technology
The University of Alabama is using D-Fend Solutions as a counter-drone technology supplier for campus and game-day airspace security. The University integrates D-Fend’s EnforceAir into its Emergency Operations Center (EOC), utilizing a unified command framework to collaborate with local, state, and federal partners during major events.
Read More →
Motorola Solutions Now Part of the Cyber Threat Alliance
Motorola Solutions is now part of the Cyber Threat Alliance, the first formally organized nonprofit group of cybersecurity practitioners that work together in good faith to share threat information and improve global defenses against advanced cyber adversaries.
Read More →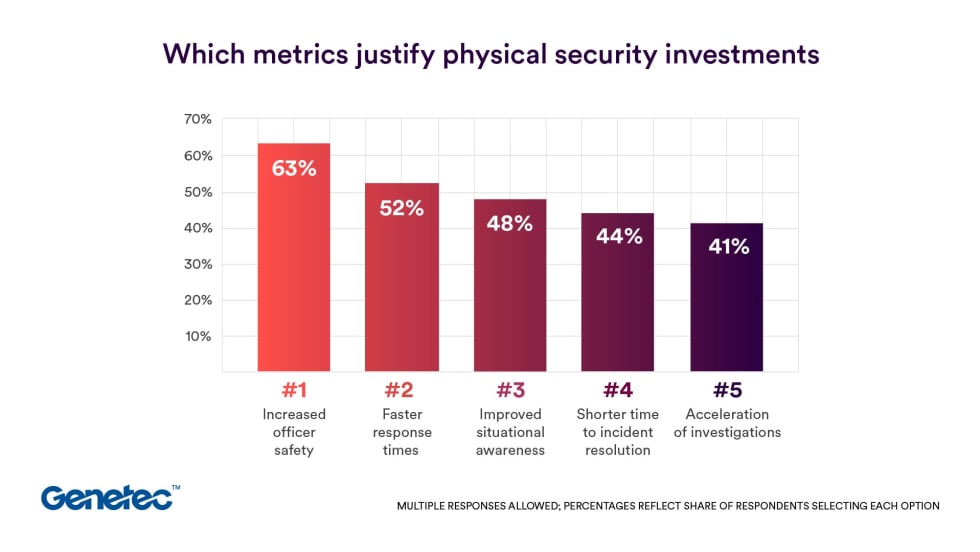
Genetec 2026 State of Physical Security Report Reveals Public Safety Priorities & Challenges
Survey results from Genetec’s 2026 State of Physical Security Report highlight the demand for integrated systems that improve response times and reduce investigative workload. Nearly nine in 10 respondents said they use security data to help keep officers safe.
Read More →



